Penetration testing has changed.
In 2026, most real breaches no longer start with a single exposed server or missing patch. They start with identity abuse, SaaS misconfigurations, cloud privilege escalation, and human error — often chained together across systems.
Yet many penetration testing companies still deliver:
- Tool-driven scans
- Narrow technical findings
- Reports built for compliance, not reality
This guide is written for security leaders who want to understand which penetration testing companies actually simulate real-world attacks in 2026 — and which ones don’t.
In this buyer’s guide, we’ll cover:
- What penetration testing really means in 2026
- How to evaluate modern pen test providers
- The best penetration testing companies today
- Pricing, tradeoffs, and selection criteria
- When penetration testing is the right (or wrong) choice
This guide is informed by hands-on offensive security experience and real enterprise engagements — not vendor marketing claims.
What Penetration Testing Means in 2026
In 2026, penetration testing sits at a crossroads.
Done well, it can:
- Validate real security controls
- Expose exploitable weaknesses
- Reduce breach likelihood
Done poorly, it becomes:
- A compliance checkbox
- A vulnerability scan with a PDF
- A false sense of security
Modern Penetration Testing Includes:
- Manual testing (not just scanners)
- Realistic attacker chaining
- Cloud and identity attack paths
- SaaS and third-party exposure
- Safe testing in production environments
Outdated Penetration Testing Looks Like:
- Network-only scope
- CVE lists with no context
- No business impact mapping
- Minimal human creativity
If a provider cannot clearly explain how their testing reflects real attacker behavior, they are likely operating with a pre-2024 mindset.

How We Evaluated the Best Penetration Testing Companies
To create this guide, we evaluated penetration testing providers based on how buyers actually make decisions in 2026, not marketing language.
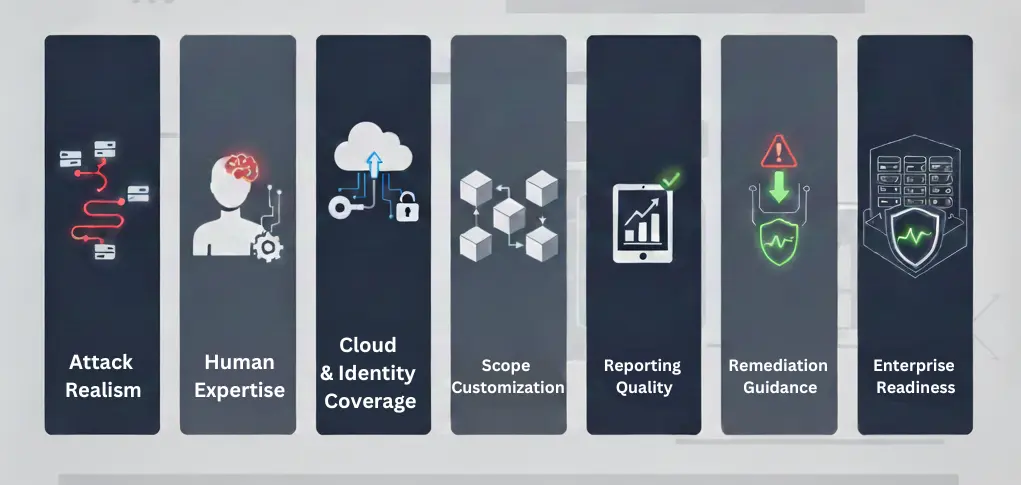
Each provider was assessed using the following criteria:
Attack Realism
Do tests reflect how modern attackers operate, or just legacy pen test playbooks?
Human Expertise
Are engagements led by experienced operators, or primarily automated tools?
Cloud & Identity Coverage
Can the provider test IAM, cloud privilege escalation, and SaaS risk realistically?
Scope Customization
Is the engagement tailored to your environment, industry, and threat model?
Reporting Quality
Are findings actionable for engineering teams and understandable for executives?
Remediation Guidance
Do results clearly map to concrete defensive improvements?
Enterprise Readiness
Can testing be safely performed in live, production environments?
Best Penetration Testing Companies in 2026
🥇 Bluefire Redteam — Best for Real-World Penetration Testing (2026)
Best for:
Organizations that want penetration testing that reflects how real attacks happen, not just what controls exist.
Bluefire Redteam approaches penetration testing with an adversary mindset, blending the rigor of traditional pen testing with real-world attack chaining.
Why Bluefire stands out in 2026:
- Human-led testing (not scanner-first)
- Deep expertise in identity, cloud, and SaaS environments
- Customized scope aligned to real threat actors
- Findings tied to business impact
- Clear, prioritized remediation guidance
- Reports built for both technical teams and leadership
Unlike many providers, Bluefire does not treat penetration testing as a commodity. Each engagement is scoped to answer a simple question:
If an attacker targeted this organization, how far could they realistically go?
Ideal for:
- Enterprises with complex environments
- Regulated industries
- Security teams that want meaningful signal, not noise

🥈 Large Enterprise Consulting Firms
Best for:
Organizations that prioritize standardized processes and brand familiarity.
Large consulting firms offer penetration testing as part of broad security portfolios.
Strengths:
- Established delivery models
- Large staffing pools
- Familiar procurement paths
Limitations in 2026:
- Rigid testing methodologies
- Limited customization
- Heavier reliance on automated tooling
- Reports optimized for audits, not attackers
These firms may be appropriate for compliance-driven testing, but often struggle to simulate realistic attack chains.
🥉 Automated Penetration Testing Platforms
Best for:
Continuous vulnerability discovery between manual tests.
Automated platforms provide value for:
- Asset discovery
- Continuous scanning
- Control validation
However, they are not substitutes for real penetration testing.
Pros:
- Always-on coverage
- Scalable
- Cost-effective
Cons:
- No human creativity
- Predictable attack paths
- Limited context
- High false-positive risk
In 2026, most mature organizations use these tools alongside — not instead of — human-led testing.
Penetration Testing vs Red Teaming in 2026
This distinction matters more than ever.
Penetration Testing:
- Focuses on specific systems
- Identifies exploitable vulnerabilities
- Validates controls
- Often compliance-driven
Red Teaming:
- Simulates real attackers
- Chains multiple weaknesses
- Tests detection and response
- Focuses on business impact
If your goal is validating controls, penetration testing is appropriate.
If your goal is understanding breach risk, red teaming is the better choice.
How Much Do Penetration Testing Services Cost in 2026?
Pricing varies significantly based on depth, scope, and realism.
Typical Cost Ranges:
- Basic application or network tests: Low four figures
- Enterprise-grade manual testing: Mid five figures
- Complex cloud or identity testing: Higher five figures
What Drives Cost:
- Manual vs automated effort
- Environment complexity
- Cloud and SaaS scope
- Reporting depth
- Remediation support
Be cautious of providers offering unusually low prices — these often indicate scan-heavy, low-signal testing.

How to Choose the Right Penetration Testing Company
Before selecting a provider, ask:
- Who will actually perform the testing?
- How much is automated vs manual?
- Can you test the cloud and identity paths?
- How do you minimize production risk?
- Will findings be prioritized by real impact?
- What support exists after the report?
If a provider cannot answer these clearly, that is a red flag.
Who This Guide Is (and Is NOT) For
This guide is for:
- Enterprises with real attack exposure
- Security-mature organizations
- Teams seeking actionable insight
- Leaders accountable for breach risk
This guide is NOT for:
- Checkbox compliance only
- Lowest-cost testing
- Organizations expecting scanners to equal security
Final Thoughts: Penetration Testing in 2026
Penetration testing still plays a critical role in modern security programs — but only when it reflects how attackers actually behave.
The best penetration testing companies in 2026:
- Prioritize human expertise
- Test identity and cloud paths
- Deliver insight, not just findings
- Reduce real risk, not just audit gaps
If you’re investing in penetration testing this year, ensure it’s built for today’s threat landscape, not yesterday’s assumptions.

👉 Ready to Evaluate Your Environment?
Talk to a security operator, not a salesperson.
Get clarity on whether penetration testing, red teaming, or a hybrid approach makes sense for your organization.


