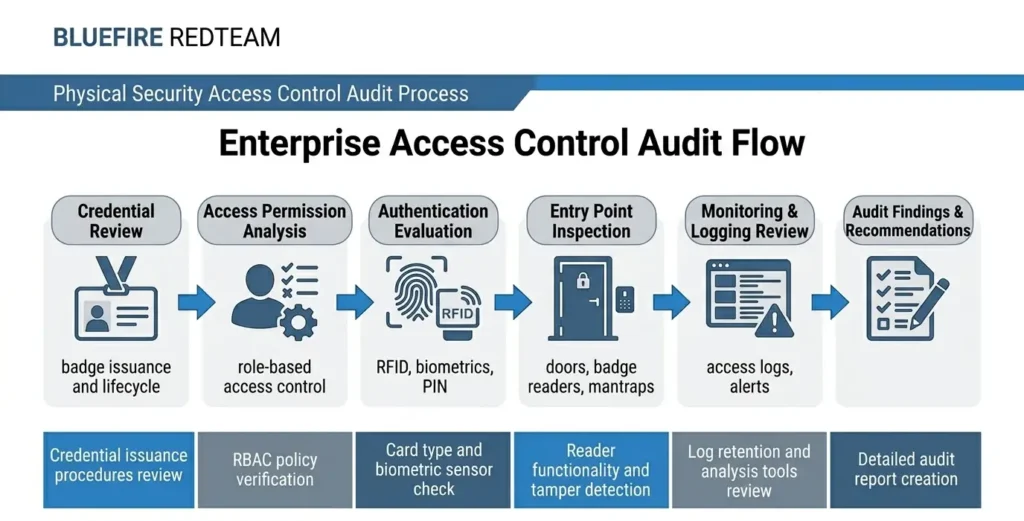
An access control audit is a structured evaluation of an organization’s physical access control systems, policies, and procedures to ensure that only authorized individuals can enter restricted areas. It assesses how access credentials, authentication mechanisms, and enforcement processes are implemented and whether they align with security requirements.
Access control audits are commonly used to validate compliance, identify security gaps, and ensure that access permissions are appropriately managed across facilities.
Why Access Control Audits Matter
Access control systems are a primary defense against unauthorized physical entry. However, even well-designed systems can fail due to misconfiguration, weak enforcement, or human behavior.
Organizations conduct access control audits to:
- Identify gaps in credential management
- Detect excessive or inappropriate access privileges
- Evaluate badge and authentication systems
- Ensure compliance with security policies
- Reduce insider and external intrusion risk
Without regular audits, access control systems may drift from intended security standards.
What an Access Control Audit Evaluates
A comprehensive access control audit reviews both technical systems and operational processes.
Access Credentials
- Badge issuance and lifecycle management
- Credential duplication risks
- Lost or unreturned badges
- Role-based access assignment
Authentication Methods
- RFID or smart card usage
- Multi-factor authentication implementation
- Biometric systems
- PIN-based access controls
Access Permissions
- Role-based access control (RBAC)
- Privilege assignment accuracy
- Access to restricted zones
- Temporary and contractor access
Physical Entry Points
- Badge reader placement
- Door access configurations
- Mantrap systems
- Emergency exit controls
Monitoring and Logging
- Access log collection
- Real-time monitoring
- Alerting for unusual access patterns
- Audit trail integrity
Policy Enforcement
- Badge usage compliance
- Tailgating prevention
- Visitor management procedures
- Escort policy enforcement
Access Control Audit vs Physical Penetration Testing
An access control audit evaluates whether systems and policies are correctly implemented.
A physical penetration test evaluates whether those controls can be bypassed.
| Access Control Audit | Penetration Testing |
|---|---|
| Reviews configuration | Simulates attacks |
| Policy-focused | Adversary-focused |
| Identifies gaps | Exploits gaps |
| Compliance-driven | Risk-driven |
Organizations often conduct audits first, followed by physical penetration testing services to validate real-world effectiveness.
Common Issues Identified in Access Control Audits
Access control audits frequently uncover:
- Excessive access privileges
- Unrevoked credentials for former employees
- Weak badge enforcement
- Shared or duplicated credentials
- Poor visitor access controls
- Lack of multi-factor authentication
- Inadequate monitoring of access logs
These issues often contribute to broader physical security vulnerabilities.
Many organizations are unaware of how access control weaknesses can be exploited in practice.
See how an access control system was fully bypassed using badge cloning
Access Control Audits and Insider Threat
Access control audits play a critical role in reducing insider threat risk.
By identifying:
- Privilege misuse potential
- Over-permissioned users
- Inadequate access reviews
- Lack of segmentation
Organizations can significantly reduce the risk of internal security breaches.
Read More: Insider Threat in Physical Security
Access Control Audits in Data Centers
Data centers require strict access control validation due to the sensitivity of infrastructure.
Audits typically focus on:
- Multi-factor authentication enforcement
- Mantrap security systems
- Server cage access restrictions
- Contractor access control
- Real-time monitoring
Read More: Data Center Physical Security Controls
How Often Should Access Control Audits Be Conducted?
Organizations should perform access control audits:
- Annually as part of security reviews
- After major staffing changes
- When implementing new access systems
- Following security incidents
- During compliance cycles
Regular audits ensure access controls remain aligned with risk.
From Audit to Real-World Validation
While access control audits identify configuration and policy gaps, they do not test real-world exploitation.
Organizations seeking deeper validation should conduct:
These simulate realistic intrusion scenarios to test whether access controls can be bypassed.
Best Practices for Access Control Audits
Organizations should:
- Implement role-based access control
- Conduct regular access reviews
- Use multi-factor authentication
- Monitor access logs continuously
- Enforce strict badge policies
- Integrate audits with penetration testing
Related Physical Security Terms
- Physical Security Risk Assessment
- Physical Penetration Testing
- Physical Red Teaming
- Insider Threat
- Mantrap Security System
- Badge Cloning
FAQ - Access control audit
- Frequently Asked Questions
An access control audit ensures that only authorized individuals have access to specific areas and that permissions are correctly assigned and enforced.
- What systems are reviewed during an access control audit?Audits review badge systems, authentication methods, access permissions, entry points, monitoring systems, and security policies.
- How often should access control permissions be reviewed?Access permissions should be reviewed regularly, typically quarterly or annually, and immediately after role changes or employee departures.
- Can an access control audit detect insider threats?Yes. Audits can identify excessive access privileges, improper permissions, and policy violations that may contribute to insider risk.
- What happens after an access control audit?Organizations receive a report outlining identified gaps, risk areas, and recommendations to improve access control systems and policies.

