A physical security risk assessment is a structured process used to identify, evaluate, and prioritize risks related to unauthorized physical access, facility vulnerabilities, and security control weaknesses. It helps organizations understand how physical threats could impact operations, infrastructure, and sensitive assets.
Unlike checklist-based audits, a physical security risk assessment focuses on real-world exposure, combining threat modeling, vulnerability identification, and impact analysis to guide security decision-making.
Why Physical Security Risk Assessments Matter
Organizations rely on physical security risk assessments to:
- Identify weaknesses in facility security controls
- Evaluate access control effectiveness
- Understand insider and external threat exposure
- Prioritize security investments
- Support compliance and governance requirements
Without a structured risk assessment, organizations often deploy controls without understanding whether they address actual threats.
Risk assessments identify potential vulnerabilities, but real-world testing demonstrates how those risks can be exploited.
See this RFID badge cloning case study
Key Components of a Physical Security Risk Assessment
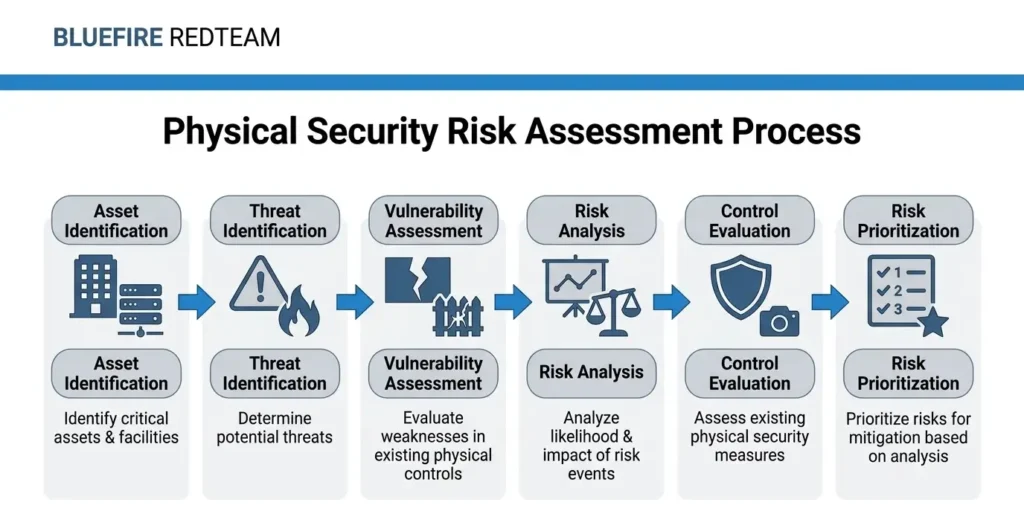
A comprehensive assessment includes several core elements:
Asset Identification
Organizations first identify critical assets such as:
- Data centers
- Server rooms
- Executive offices
- Sensitive equipment
- Intellectual property
Assets are ranked based on potential business impact.
Threat Identification
Potential threats may include:
- External intruders
- Insider threats
- Social engineering attacks
- Credential misuse
- Organized adversaries
Threat modeling helps define realistic attack scenarios.
Vulnerability Assessment
This stage identifies weaknesses such as:
- Weak badge enforcement
- Tailgating vulnerabilities
- Poor visitor management
- Unsecured restricted zones
- Lack of monitoring or response
Risk Analysis
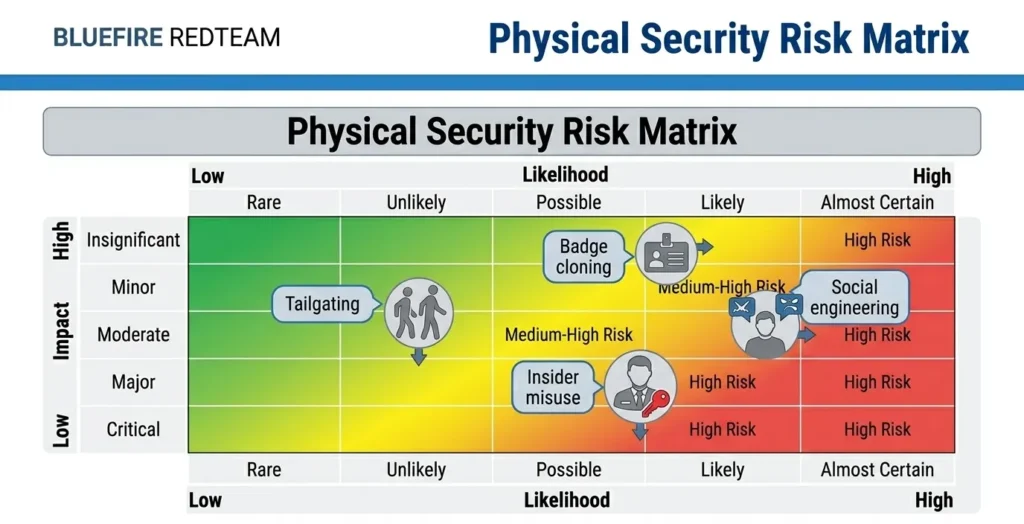
Each risk is evaluated based on:
- Likelihood of occurrence
- Potential impact
- Ease of exploitation
This allows organizations to prioritize remediation.
Control Evaluation
Existing controls are reviewed, including:
- Access control systems
- Surveillance monitoring
- Guard procedures
- Mantrap enforcement
- Security policies
Physical Security Risk Assessment vs Physical Penetration Testing
A physical security risk assessment identifies potential risks.
A physical penetration test validates whether those risks can actually be exploited.
| Assessment | Penetration Testing |
|---|---|
| Identifies risks | Exploits risks |
| Analytical | Operational |
| Predictive | Real-world simulation |
| Prioritizes controls | Tests effectiveness |
Organizations often use both together.
Common Risks Identified
Typical findings include:
- Unchallenged unauthorized individuals
- Badge sharing and cloning risks
- Weak access segmentation
- Poor surveillance monitoring
- Insider privilege misuse
- Inadequate after-hours controls
These risks often form part of larger attack paths.
Read More: Attack Path Analysis in Red Teaming
How Organizations Use Risk Assessments
Enterprises use physical security risk assessments to:
- Design a new facility security
- Improve existing controls
- Prepare for compliance audits
- Support executive decision-making
- Guide red team engagements
Organizations operating across multiple regions often standardize risk assessments across facilities.
Physical Security Risk Assessment in Data Centers
Data centers require advanced risk assessments due to:
- High-value infrastructure
- Continuous operation requirements
- Strict compliance standards
Key focus areas include:
- Perimeter access
- Mantrap systems
- Server cage protection
- Insider access control
Read More: Data Center Physical Security Controls
Best Practices for Effective Risk Assessments
Organizations should:
- Conduct assessments regularly
- Include insider threat scenarios
- Combine with penetration testing
- Prioritize high-impact risks
- Continuously update threat models
When Should You Conduct a Risk Assessment?
- Before launching new facilities
- After major security incidents
- During compliance cycles
- When implementing new access controls
- Before red team engagements
From Risk Assessment to Real-World Validation
While risk assessments identify potential vulnerabilities, organizations must validate whether those risks can be exploited.
This is where:
Become critical.
Related Physical Security Terms
- What Is Physical Penetration Testing?
- What Is Physical Red Teaming?
- What Is Threat Modeling in Physical Security?
- Attack Path Analysis in Red Teaming
- Insider Threat in Physical Security
FAQ - Physical Security Risk Assessment
- What does a physical security risk assessment include?A physical security risk assessment includes asset identification, threat modeling, vulnerability analysis, and evaluation of existing security controls to determine risk exposure.
- How is a physical security risk assessment conducted?
It is conducted by analyzing facilities, identifying potential threats, evaluating vulnerabilities, and assessing how existing controls perform against realistic attack scenarios.
- Who should perform a physical security risk assessment?Assessments should be conducted by experienced security professionals with expertise in physical security, threat modeling, and risk analysis methodologies.
- Who should perform a physical security risk assessment?The outcome is a prioritized list of risks, along with recommendations to improve physical security controls and reduce vulnerability exposure.
- How is risk assessment different from a security audit?A risk assessment focuses on identifying and prioritizing real-world threats, while an audit focuses on verifying compliance with policies and standards.

