A visitor management system (VMS) is a process or technology used to track, manage, and control visitor access within a facility. It ensures that all non-employees entering the premises are properly identified, authorized, and monitored throughout their visit.
Visitor management systems play a critical role in physical security by preventing unauthorized access, enforcing escort policies, and maintaining accurate visitor logs for security and compliance purposes.
Why Visitor Management Systems Are Important
Visitors represent one of the most common entry points for physical security breaches.
Without proper controls, visitors may:
- Access restricted areas
- Bypass access control systems
- Facilitate insider-assisted attacks
- Exploit social engineering opportunities
Organizations implement visitor management systems to:
- Track all visitor activity
- Enforce identity verification
- Prevent unauthorized access
- Improve audit and compliance readiness
- Strengthen facility security posture
How a Visitor Management System Works
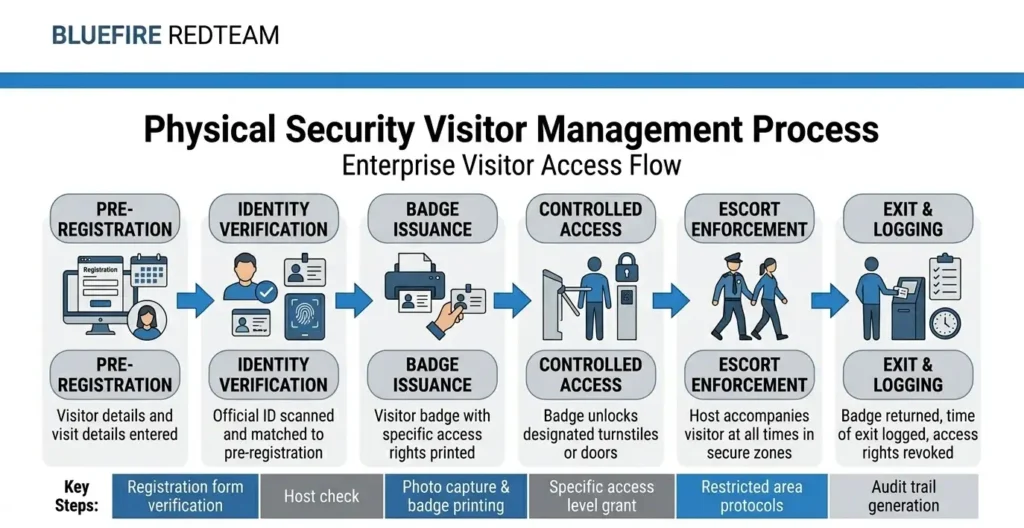
A typical visitor management process includes:
1. Pre-Registration
Visitors are registered in advance through:
- Online systems
- Host approval workflows
- Scheduled visit requests
2. Identity Verification
Upon arrival, visitors:
- Present identification
- Confirm the purpose of the visit
- Are validated against approved lists
3. Badge Issuance
Visitors receive temporary credentials that:
- Identify them as visitors
- Limit access permissions
- Expire after the visit
Attackers often exploit trust and weak verification processes to gain access.
See how access systems were bypassed in a real-world case study
4. Access Control Integration
Visitor access may be restricted to:
- Specific floors or zones
- Designated meeting areas
- Approved time windows
5. Escort Enforcement
Visitors are typically required to:
- Be accompanied by authorized employees
- Avoid accessing restricted areas independently
6. Logging and Monitoring
Visitor management systems track:
- Entry and exit times
- Movement within the facility
- Access attempts
- Host responsibility
Visitor Management Systems vs Access Control Systems
Access control systems manage employee access.
Visitor management systems manage temporary and external access.
| Access Control | Visitor Management |
|---|---|
| Employee-focused | Visitor-focused |
| Long-term credentials | Temporary credentials |
| Role-based access | Limited, supervised access |
| Continuous usage | Time-bound access |
Both systems must work together to maintain security.
Read more: What Is an Access Control Audit?
Common Vulnerabilities in Visitor Management
Visitor-related security gaps often include:
- Lack of identity verification
- Visitors not logged or tracked
- Weak escort enforcement
- Temporary badges not collected
- Visitors accessing unauthorized areas
- Poor coordination between reception and security teams
These vulnerabilities are frequently identified during physical penetration testing services.
Visitor Management and Social Engineering
Visitor systems are often targeted in social engineering attacks.
Attackers may:
- Pose as contractors or vendors
- Claim urgent access needs
- Exploit busy reception environments
- Use convincing pretexts to gain entry
Read More: Social Engineering in Physical Security
Strong visitor management reduces these risks significantly.
Visitor Management in Data Centers
Data centers require strict visitor controls due to:
- High-value infrastructure
- Regulatory requirements
- Continuous operations
Typical controls include:
- Pre-approved visitor lists
- Identity verification
- Mandatory escorts
- Restricted zone access
- Real-time monitoring
Read more: Data Center Physical Security Controls
Visitor Management and Insider Threat
Visitors can become insider threat vectors when:
- Employees fail to enforce escort policies
- Visitors are granted excessive access
- Temporary credentials are misused
Visitor management must be tightly integrated with access control policies.
Read more: Insider Threat in Physical Security
Best Practices for Visitor Management Systems

Organizations should:
- Implement digital visitor management systems
- Require identity verification for all visitors
- Enforce strict escort policies
- Limit access to necessary areas only
- Track visitor activity in real time
- Collect and deactivate temporary badges
- Conduct regular security testing
How Visitor Management Systems Are Tested
Visitor management controls are often evaluated through:
- Social engineering simulations
- Unauthorized access attempts
- Escort policy testing
- Badge misuse scenarios
These tests are part of:
When Should Organizations Upgrade Visitor Management?
Organizations should improve visitor management when:
- Scaling operations or facilities
- Experiencing security incidents
- Preparing for compliance audits
- Implementing new access control systems
- Expanding into high-security environments
Related Physical Security Terms
- What Is an Access Control Audit?
- What Is a Physical Security Risk Assessment?
- Social Engineering in Physical Security
- Insider Threat in Physical Security
- What Is Physical Penetration Testing?
- What Is a Mantrap Security System?
FAQ - Visitor Management System
- What is a visitor management system used for?A visitor management system is used to track, verify, and control visitor access to ensure only authorized individuals enter a facility.
- Do all organizations need a visitor management system?
Most organizations with physical offices benefit from visitor management systems, especially those handling sensitive data or critical infrastructure.
- Can visitor management systems prevent social engineering?They significantly reduce risk by enforcing identity verification, access control, and escort policies, though additional security measures are also required.
- What happens if visitors are not properly managed?Poor visitor management can lead to unauthorized access, data exposure, insider risk, and compliance violations.
- Are digital visitor management systems better than manual logs?Yes. Digital systems provide better tracking, audit trails, real-time monitoring, and integration with access control systems.

