Customer Overview
A leading UAE-based conglomerate with a diverse portfolio of 15+ companies, operating across sectors including automotive, construction, and corporate services.
The organization operates at enterprise scale with:
- 600+ employees across multiple business units
- Independent companies with shared services
- Centralized email and communication infrastructure
- High inter-company collaboration and trust-based workflows
Due to its size and structure, the group represents a high-value target for phishing attacks and Business Email Compromise (BEC).
The Challenge
Despite having standard cybersecurity controls and awareness initiatives in place, leadership lacked clear visibility into:
- Real-world employee susceptibility to phishing attacks
- Exposure to Business Email Compromise (BEC)
- Risk across high-value roles such as Finance, HR, and Executives
- Variations in security maturity across group companies
The key question was:
“If a real phishing attack targeted our organization today — how would our people respond?”
Engagement Objective
Bluefire Redteam was engaged to conduct an enterprise-wide phishing simulation to:
- Measure human-layer security risk
- Identify high-risk users, roles, and business units
- Simulate real-world attacker techniques
- Benchmark results against industry standards
- Provide a clear roadmap for risk reduction
Approach & Methodology
To replicate real-world attack scenarios, Bluefire Redteam designed a controlled phishing simulation campaign using advanced social engineering techniques.
Key Elements of the Simulation
- Targeted 602 employees across all companies
- Use of authority-based and compliance-driven lures
- Deployment of a lookalike phishing domain to mimic real attackers
- Microsoft Office-style phishing forms
- No malware or real credential harvesting (fully controlled environment)
Attack Scenarios Simulated
1. Executive Authority Phishing
- CEO-themed communication
- Incentive-based messaging (gift registration)
- Time-sensitive action request
Designed to exploit trust in leadership and urgency
2. HR Policy Compliance Phishing
- Mandatory policy acknowledgment
- Routine internal communication style
- Familiar HR workflow
Designed to exploit process trust and employee behavior patterns
Key Results
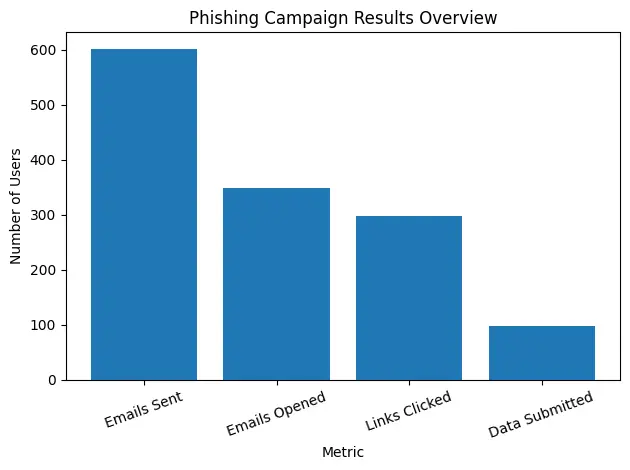
The results highlighted a significant human-layer security gap:
- 602 emails sent
- 57.97% email open rate
- 49.67% of users clicked the phishing link
- 16.28% submitted sensitive information
- 65.95% overall failure rate
Industry Benchmark Comparison
| Metric | Client Result | Industry Average | Risk Level |
|---|---|---|---|
| Email Open Rate | 57.97% | 25–35% | High |
| Click Rate | 49.67% | 8–12% | Critical |
| Data Submission | 16.28% | 3–6% | Severe |
| Failure Rate | 65.95% | 10–15% | High |
The organization’s phishing susceptibility was 4–5 times higher than industry benchmarks
Key Findings
1. Enterprise-Wide Exposure
Phishing risk was not isolated; it was consistent across multiple companies within the group.
2. High-Risk Roles Identified
- Finance Teams → Critical fraud risk
- Executives → Vulnerable to authority-based attacks
- HR Teams → Susceptible to compliance-themed phishing
3. Trust as a Vulnerability
Employees were more likely to engage with phishing emails when:
- The email appeared to come from internal leadership or HR
- The domain looked similar to the legitimate one
- The request matched routine business processes
Potential Business Impact
If this simulation had been a real attack, the organization could have faced:
- Email account compromise
- Internal phishing propagation
- Payroll and invoice fraud
- Unauthorized access to SaaS platforms
- Reputational and regulatory consequences
Strategic Insights
This engagement revealed a critical reality:
Cybersecurity risk was not limited to technology, it was heavily driven by human behavior.
For large conglomerates, this risk is amplified due to:
- Interconnected business units
- Shared trust environments
- High-value financial and operational workflows
Remediation Strategy
Bluefire Redteam provided a structured roadmap to reduce phishing risk:
Immediate Actions (0–30 Days)
- Targeted phishing awareness for affected users
- Deployment of phishing reporting mechanisms
- Domain verification and awareness training
Short-Term Actions (30–90 Days)
- Role-based phishing simulations (Finance, HR, Executives)
- Quarterly phishing benchmarking
- Executive-focused security training
Long-Term Strategy (90+ Days)
- Continuous phishing simulation program
- Human risk scoring across business units
- Integration of phishing metrics into SOC monitoring
Target Outcomes (12 Months)
| Metric | Current | Target |
|---|---|---|
| Click Rate | 49.67% | < 5% |
| Data Submission | 16.28% | < 1% |
| Failure Rate | 65.95% | < 7% |
Conclusion
The phishing simulation demonstrated that even large, well-established enterprises remain highly vulnerable to social engineering attacks.
Without continuous testing and targeted training:
Human error can become the easiest entry point for attackers.
About Bluefire Redteam
Bluefire Redteam specializes in real-world attack simulations, penetration testing, and human risk assessments to help organizations identify and mitigate security gaps before attackers exploit them.
Read more customer stories

