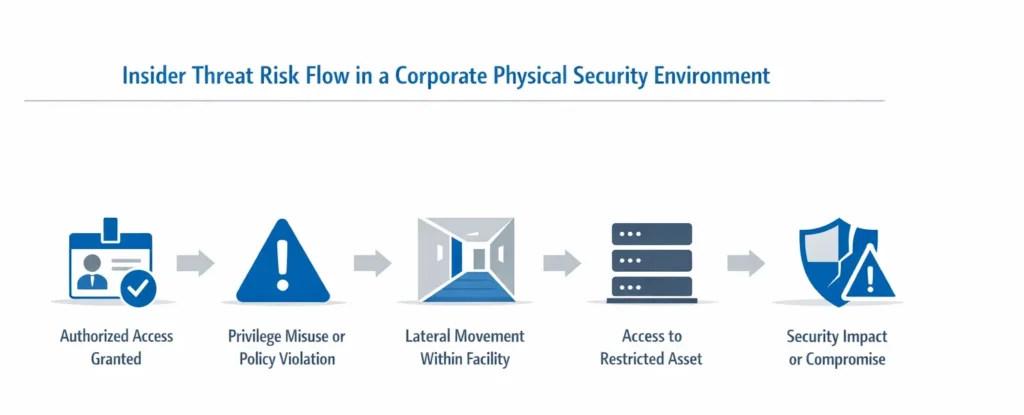
An insider threat in physical security refers to the risk posed by individuals with authorized access to facilities, systems, or sensitive areas who misuse their privileges to cause harm, intentionally or unintentionally. Unlike external attackers, insiders already possess legitimate credentials, knowledge of security procedures, and familiarity with facility layouts.
Because insiders operate within trusted boundaries, they are often more difficult to detect than external intruders.
In enterprise environments, insider threat represents one of the most complex physical security risks to manage.
What Is an Insider Threat?
An insider threat involves a current or former employee, contractor, vendor, or partner who has authorized physical access and uses that access in a way that compromises security.
Insider threats may be:
- Malicious (intentional harm)
- Negligent (careless behavior)
- Compromised (coerced or manipulated)
- Opportunistic (abusing weak oversight)
Physical insider threats often intersect with cybersecurity risk.
Types of Insider Threats in Physical Security
Malicious Insider
An individual who deliberately attempts to:
- Steal hardware or sensitive information
- Sabotage equipment
- Provide access to external attackers
- Circumvent physical controls
This type poses high-impact risk.
Negligent Insider
An employee who:
- Shares access badges
- Holds doors open for unauthorized individuals
- Fails to report suspicious activity
- Ignores escort policies
Negligence is one of the most common insider vulnerabilities.
Compromised Insider
An employee manipulated through:
- Social engineering
- Coercion
- Financial pressure
- Credential phishing
External actors often rely on compromised insiders to simplify attack paths.
Privilege Abuse
An individual who exceeds authorized access levels, such as:
- Entering restricted zones without business need
- Accessing server cages outside assigned responsibilities
- Abusing administrative privileges
Poor role-based access controls increase this risk.
Why Insider Threat Is Difficult to Detect
Insiders already have:
- Valid credentials
- Approved access levels
- Familiarity with monitoring systems
- Knowledge of guard routines
Traditional physical security controls such as badge readers or mantraps may not prevent misuse if privileges are excessive.
Detection requires behavioral analysis, monitoring, and segmentation.
Common Physical Insider Threat Scenarios
Example 1: Credential Sharing
An employee shares an access badge with a colleague who lacks clearance.
Example 2: After-Hours Access Abuse
An individual enters a restricted area outside of normal business hours without legitimate justification.
Example 3: Hardware Removal
Authorized staff remove equipment without triggering detection due to insufficient asset monitoring.
Example 4: Facilitated External Entry
An insider intentionally assists external attackers through badge access or door bypass.
These scenarios are often uncovered during physical penetration testing services.
Insider Threat vs External Intrusion
| Factor | External Attacker | Insider Threat |
|---|---|---|
| Access Credentials | No | Yes |
| Knowledge of Facility | Limited | High |
| Monitoring Awareness | Limited | High |
| Detection Difficulty | Moderate | High |
| Risk Severity | High | Often Critical |
Insiders often reduce the number of barriers required in an attack path.
This is why insider threat must be considered during attack path analysis in red teaming.
Insider Threat in Data Centers
Data centers face elevated insider risk due to:
- Concentrated critical infrastructure
- Role-based access privileges
- Contractor access
- Hardware-level attack potential
Common data center insider risks include:
- Server cage misuse
- Badge sharing
- Unauthorized hardware access
- Power system interference
Learn more about data center physical security controls.
How Physical Red Teaming Evaluates Insider Risk
Advanced physical red team engagements may simulate:
- Credential misuse scenarios
- Insider-facilitated access
- Policy bypass attempts
- Privilege escalation pathways
- Combined insider + external attack paths
This testing identifies whether detection systems catch anomalous behavior.
Key Indicators of Physical Insider Threat
Organizations should monitor:
- Repeated access to non-assigned zones
- Access outside of normal hours
- Attempts to disable surveillance
- Tailgating within restricted zones
- Excessive access privileges
- Unusual badge activity patterns
Behavioral anomalies often precede major incidents.
Preventing Insider Threat in Physical Security
Mitigation requires layered controls:
Role-Based Access Control
Limit access strictly to job responsibilities.
Segmentation
Restrict movement between zones.
Access Log Monitoring
Actively review badge logs and anomalies.
Multi-Factor Authentication
Reduce single-point credential abuse.
Strict Visitor Policies
Prevent insider-facilitated external access.
Recurring Physical Penetration Testing
Validate that insider scenarios are detected.
Insider Threat and Organizational Culture
Security culture plays a critical role.
Organizations must:
- Encourage reporting of suspicious behavior
- Remove stigma around raising concerns
- Reinforce accountability
- Promote shared responsibility for physical security
Culture gaps often enable insider incidents.
Executive Impact of Insider Threat
For leadership, insider threat represents:
- Reputational risk
- Regulatory exposure
- Operational disruption
- Financial loss
- Legal liability
Threat modeling in physical security should always include insider scenarios.
Learn more about threat modeling in physical security.
Insider Threat Is Not Just a Cyber Problem
Many organizations focus heavily on digital insider risk while overlooking physical exposure.
However, physical access often enables:
- Hardware implantation
- Network compromise
- Data exfiltration
- Infrastructure sabotage
Physical and cyber risk are increasingly intertwined.
Related Physical Security Terms
- What Is Physical Red Teaming?
- Attack Path Analysis in Red Teaming
- What Is Threat Modeling in Physical Security?
- Data Center Physical Security Controls
- What Is Physical Penetration Testing?
Insider Threat in Physical Security - Frequently Asked Questions
- What is considered an insider threat in physical security?An insider threat in physical security involves a person with authorized access who intentionally or unintentionally misuses their privileges, creating risk to facilities, infrastructure, or sensitive areas.
- Are insider threats always malicious?
No. Insider threats can be malicious, negligent, or accidental. Many incidents occur due to policy violations, credential sharing, or failure to follow access procedures.
- How can organizations detect insider threats?
Detection requires access log monitoring, behavioral anomaly analysis, strict role-based access controls, and recurring physical penetration testing to validate control effectiveness.
- Why are insider threats difficult to prevent?
Insiders already have legitimate credentials and knowledge of facility operations, making misuse harder to detect than external intrusion attempts.
- How does red teaming evaluate insider threat risk?Physical red team engagements simulate credential misuse, privilege escalation, and insider-assisted intrusion scenarios to assess detection and response capabilities.

