Social engineering in physical security is a manipulation-based attack technique in which an individual exploits human behavior, trust, or authority to gain unauthorized physical access to restricted areas. Unlike technical hacking methods, social engineering relies on psychological tactics rather than system vulnerabilities.
In enterprise environments, social engineering is one of the most common and effective physical intrusion methods identified during physical penetration testing and red team engagements.
What Is Social Engineering?
Social engineering is a deception-based strategy used by attackers to persuade individuals to bypass security controls voluntarily.
In physical security contexts, this may involve:
- Pretending to be a contractor
- Impersonating IT support
- Claiming urgency or authority
- Requesting access under false pretenses
- Exploiting employee politeness
Rather than forcing entry, the attacker convinces someone to allow access.
How Social Engineering Works in Physical Environments
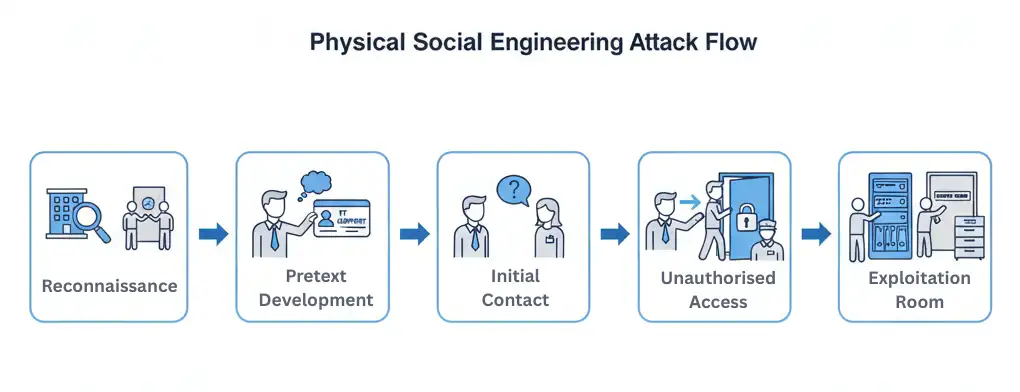
Physical social engineering attacks typically follow a predictable pattern:
1. Reconnaissance
The attacker gathers information about:
- Employee routines
- Building layout
- Security guard schedules
- Corporate branding
- Visitor processes
2. Pretext Development
A believable scenario (pretext) is created, such as:
- “I forgot my badge.”
- “I’m from IT and need to fix a server.”
- “I’m here for a scheduled delivery.”
3. Execution
The attacker approaches employees or security staff and leverages:
- Confidence
- Authority signals
- Urgency
- Uniforms or props
4. Access Exploitation
Once inside, the attacker may:
- Move to restricted areas
- Install unauthorized devices
- Collect sensitive information
- Test response procedures
Common Types of Social Engineering in Physical Security

Tailgating
Following an authorized individual into a restricted area without presenting credentials.
Impersonation
Pretending to be a trusted role such as maintenance staff, IT personnel, or vendor representatives.
Pretexting
Creating a fabricated scenario to justify access.
Shoulder Surfing
Observing PIN entries or access code usage.
Authority Exploitation
Claiming executive authorization to bypass controls.
These tactics are frequently identified during physical red team simulations.
Why Social Engineering Is So Effective
Social engineering succeeds because it targets human psychology.
Employees often:
- Avoid confrontation
- Want to be helpful
- Trust uniforms or badges
- Assume others have been authorized
- Fail to challenge confident individuals
Even well-configured access control systems can be bypassed if human enforcement fails.
Organizations may pass a physical security audit but still be vulnerable to social engineering attacks.
Social Engineering vs Technical Access Control Attacks
Technical attacks exploit system weaknesses, such as:
- RFID cloning
- Credential duplication
- Lock bypassing
Social engineering exploits behavioral weaknesses.
Both may be tested during authorized physical penetration testing engagements.
The most resilient organizations defend against both human and technical attack vectors.
Real-World Risks of Physical Social Engineering
Successful social engineering attacks can result in:
- Unauthorized facility access
- Theft of physical devices
- Network hardware compromise
- Insider facilitation
- Data exfiltration
- Regulatory violations
High-risk environments include:
- Data centers
- Financial institutions
- Healthcare facilities
- Government offices
- Industrial plants
Global enterprises increasingly integrate adversary simulation testing to evaluate real-world vulnerability exposure.
How Physical Penetration Testing Identifies Social Engineering Weaknesses
During authorized testing engagements, red team operators may:
- Attempt entry using fabricated identities
- Request badge overrides
- Test employee challenge procedures
- Attempt delivery-based pretexting
- Evaluate guard response protocols
These controlled simulations reveal how employees respond under realistic adversary pressure.
Learn more about enterprise physical penetration testing services.
Advanced organizations also conduct comprehensive physical red team engagements to test detection and escalation processes.
How to Prevent Social Engineering Attacks
Organizations can reduce risk through:
1. Employee Awareness Training
Regular training on how to identify and challenge suspicious individuals.
2. Strict Badge Enforcement
No exceptions for “forgotten badges.”
3. Visitor Escort Policies
All non-employees must be escorted at all times.
4. Clear Escalation Procedures
Employees must know how to report suspicious behavior.
5. Recurring Physical Penetration Testing
Testing validates whether awareness training is effective in practice.
The Role of Organizational Culture
Security culture plays a critical role in resisting social engineering.
Organizations that encourage employees to:
- Politely challenge unknown individuals
- Report anomalies
- Follow protocol without exception
Are significantly more resilient.
Leadership messaging must reinforce that security enforcement is everyone’s responsibility.
Social Engineering and Insider Threat
Social engineering can also facilitate insider compromise.
An attacker may:
- Manipulate employees into sharing credentials
- Pressure staff into granting temporary access
- Recruit insiders for physical access support
These hybrid attack paths are often uncovered during structured red team exercises.
Related Physical Security Terms
- What Is Tailgating in Physical Security?
- What Is RFID Cloning?
- What Is Physical Red Teaming?
- What Is Physical Penetration Testing?
- Attack Path Analysis in Red Teaming
- Controlled Intrusion Testing Explained
- What Is Threat Modeling in Physical Security?
Social Engineering in Physical Security - FAQ
- Is social engineering illegal in physical security contexts?Unauthorized social engineering attempts are illegal. However, authorized social engineering simulations conducted under formal engagement are legal security assessments.
- What is the most common physical social engineering tactic?Tailgating is one of the most common tactics, where an unauthorized individual follows an authorized employee into a restricted area.
- How can employees prevent social engineering attacks?Employees can prevent social engineering by enforcing badge policies, challenging unknown individuals, following visitor protocols, and reporting suspicious behavior.
- How does penetration testing identify social engineering risk?Penetration testing simulates controlled social engineering scenarios to evaluate employee response, access enforcement, and detection procedures.

