Physical access control systems are security mechanisms designed to regulate and monitor who can enter specific physical spaces within a facility. These systems authenticate individuals using credentials such as keycards, biometrics, PIN codes, or mobile devices to restrict unauthorized access to buildings, rooms, and secure areas.
Modern physical access control systems are a critical component of enterprise security strategies, particularly in corporate offices, data centers, healthcare facilities, financial institutions, and industrial environments.
What Is a Physical Access Control System?
A physical access control system (PACS) is a layered security framework that:
- Verifies identity
- Grants or denies entry
- Logs access activity
- Monitors movement within secure areas
Unlike traditional mechanical locks, electronic access control systems provide centralized management, audit trails, and real-time monitoring capabilities.
They are often integrated with:
- CCTV systems
- Alarm systems
- Visitor management platforms
- Security operations centers (SOC)
How Physical Access Control Systems Work
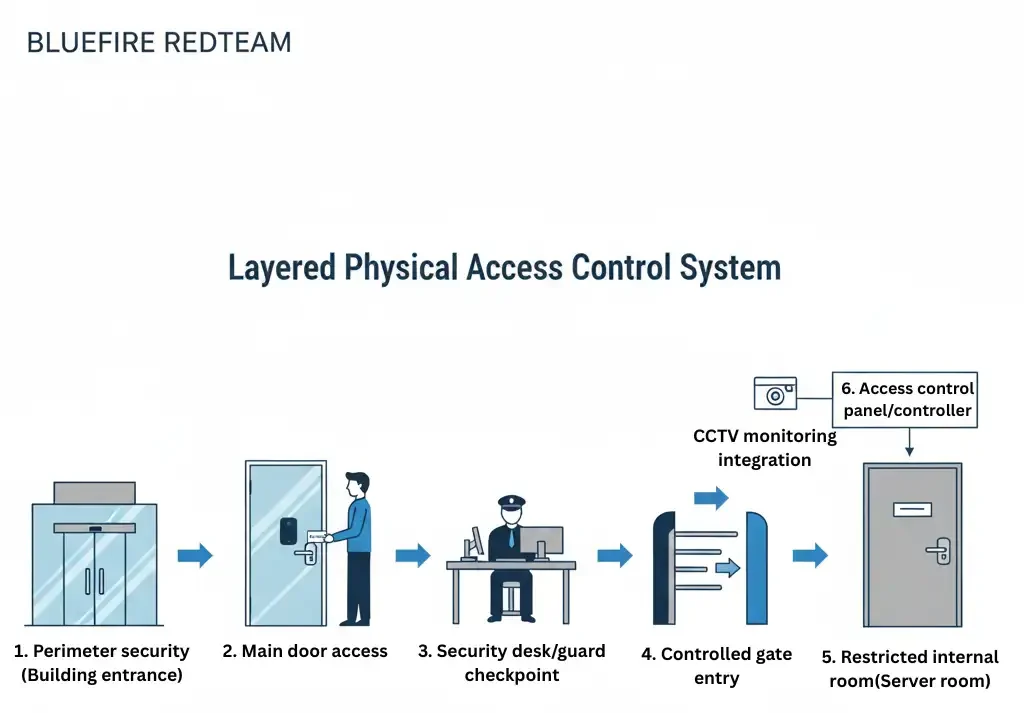
Physical access control systems typically operate through four primary components:
1. Credential
The item used to authenticate identity, such as:
- RFID badge
- Smart card
- Biometric identifier
- PIN code
- Mobile access token
2. Reader
The device that scans or verifies credentials.
Examples include:
- Proximity card readers
- Biometric scanners
- Keypad entry systems
3. Control Panel
The backend system that validates credentials and determines access permissions.
4. Locking Mechanism
The physical device that secures entry points, such as:
- Electronic door strikes
- Magnetic locks
- Turnstiles
- Mantrap systems
When a credential is presented, the system verifies authorization before granting or denying entry.
Types of Physical Access Control Systems
Organizations implement different access control models depending on risk tolerance and regulatory requirements.
Discretionary Access Control (DAC)
Access is granted at the discretion of administrators or facility managers.
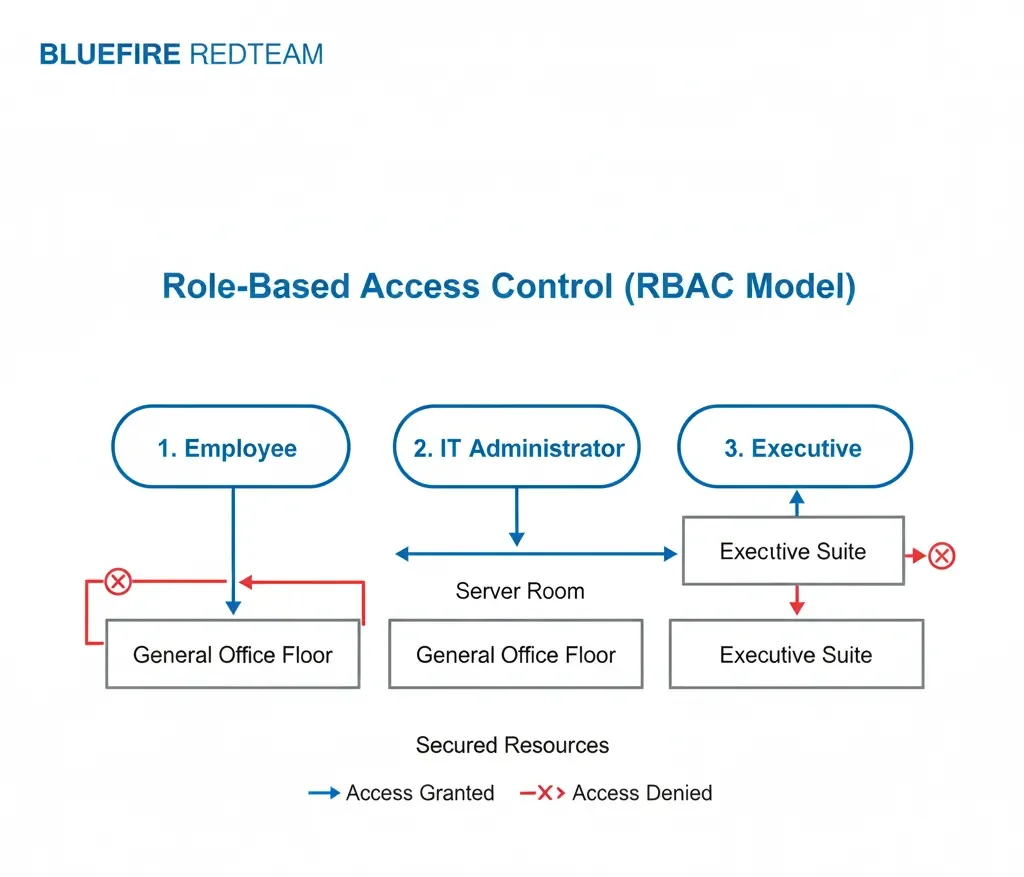
Role-Based Access Control (RBAC)
Access is assigned based on job function or role within the organization.
Mandatory Access Control (MAC)
Strict policies define access rights based on clearance levels.
Attribute-Based Access Control (ABAC)
Access decisions consider multiple contextual factors, such as time of day or device used.
Enterprise environments commonly rely on role-based and attribute-based models.
Common Access Control Technologies
Modern systems use various technologies, including:
RFID and Proximity Cards
Widely used in corporate facilities. These can be vulnerable if not encrypted properly, which may expose organizations to badge cloning attacks.
Smart Cards with Encryption
Provide stronger security using encrypted communication protocols.
Biometric Systems
Fingerprint, facial recognition, or iris scanning for high-security areas.
Mobile Access Credentials
Smartphone-based access tokens using secure digital authentication.
Why Physical Access Control Systems Are Critical for Enterprises
Access control systems protect:
- Sensitive data
- Critical infrastructure
- Executive offices
- Server rooms
- Research facilities
- Restricted industrial zones
A compromised access control system can lead to:
- Data exfiltration
- Hardware tampering
- Intellectual property theft
- Insider threat facilitation
- Regulatory violations
Organizations conducting physical penetration testing services frequently discover misconfigured or outdated access control systems.
Common Vulnerabilities in Physical Access Control Systems
Even modern systems may contain weaknesses, including:
- Unencrypted RFID credentials
- Poor badge revocation processes
- Shared access cards
- Weak monitoring of after-hours access
- Lack of multi-factor authentication
- Failure to audit access logs
These vulnerabilities are often identified during physical red team engagements.
Physical Access Control Systems vs Mechanical Locks
Mechanical locks provide static protection.
Electronic access control systems provide:
- Audit trails
- Revocation capabilities
- Remote management
- Time-based restrictions
- Real-time monitoring
However, electronic systems must be properly configured and regularly tested to ensure effectiveness.
How Physical Penetration Testing Evaluates Access Control Systems
During authorized testing engagements, security professionals may:
- Attempt credential duplication
- Test for tailgating weaknesses
- Assess reader encryption strength
- Evaluate multi-factor enforcement
- Analyze access log monitoring
- Attempt after-hours entry
These assessments validate whether the access control system functions effectively under real-world adversary simulation.
Learn more about physical penetration testing services
Best Practices for Strengthening Access Control Systems
Organizations can improve security posture by implementing:
1. Encrypted Credential Technology
Upgrade legacy low-frequency systems.
2. Multi-Factor Authentication
Combine badge access with PIN or biometrics.
3. Regular Access Reviews
Audit role-based permissions quarterly.
4. Access Log Monitoring
Actively review anomalies and unusual patterns.
5. Periodic Physical Penetration Testing
Validate controls through controlled adversary simulation.
Industries That Rely Heavily on Access Control Systems
Access control systems are especially critical in:
- Data centers
- Financial institutions
- Healthcare facilities
- Manufacturing plants
- Energy infrastructure
- Government facilities
Organizations operating across the United States, Asia, and the GCC increasingly integrate access control validation into their security programs.

