Badge cloning is a physical security attack technique in which an unauthorized individual duplicates or emulates a legitimate employee’s access credential to gain entry into restricted areas. It typically involves copying data from RFID, NFC, or proximity-based access control cards and using the cloned credential to bypass facility security systems.
Badge cloning exploits weaknesses in access control technology and credential management processes, making it a critical risk vector in enterprise environments.
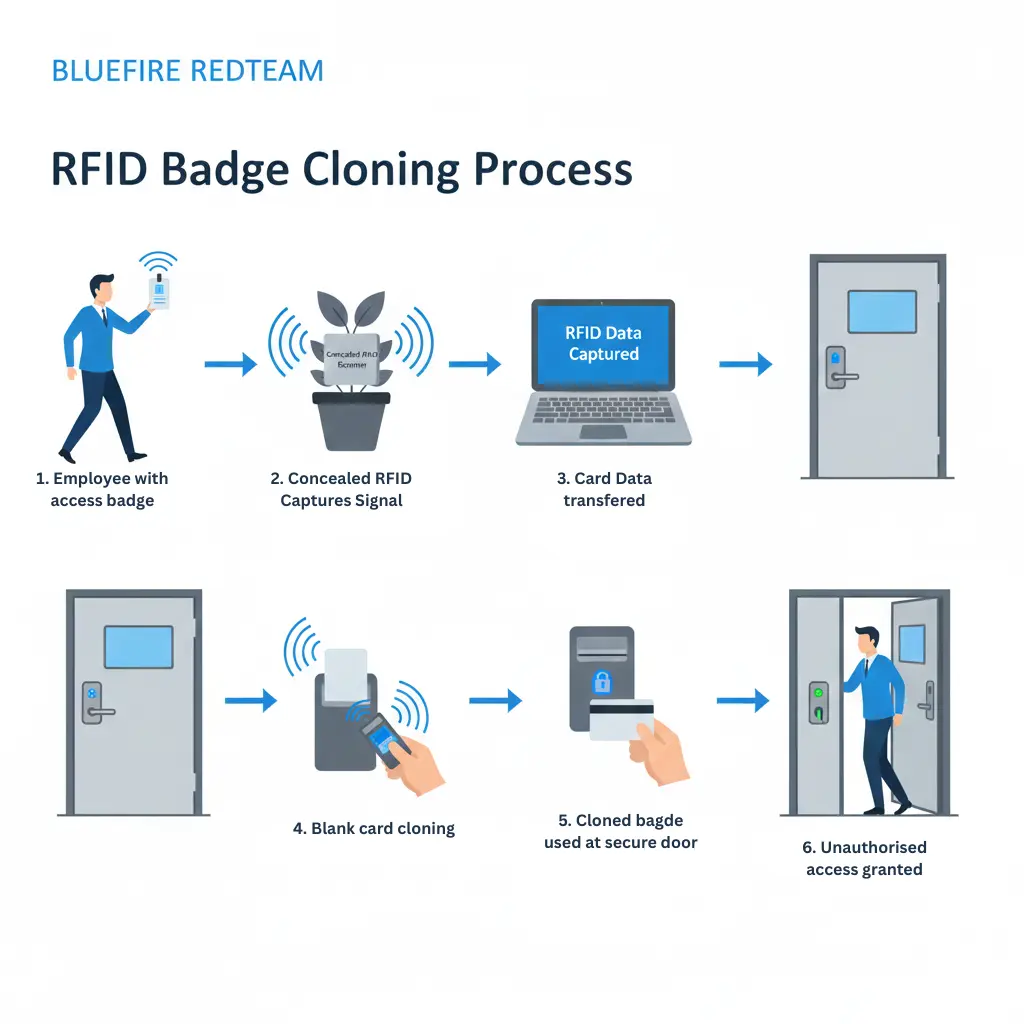
How Badge Cloning Works
Modern facilities commonly use electronic access badges that rely on:
- RFID (Radio Frequency Identification)
- NFC (Near Field Communication)
- Proximity card technology
- Smart cards
If improperly secured, these credentials can be:
- Scanned wirelessly without physical contact
- Copied onto blank cards
- Emulated using mobile devices
- Used to access secure areas undetected
Attackers may capture credential data by:
- Standing near employees in public spaces
- Using concealed RFID readers
- Exploiting outdated encryption protocols
- Targeting improperly configured access systems
Badge cloning is not just a theoretical risk. Real-world testing has shown how attackers can fully replicate access credentials and bypass physical security systems.
See how RFID badge cloning led to full access compromise
Why Badge Cloning Is a Major Enterprise Risk
A cloned badge provides the same level of access as a legitimate credential.
This can allow unauthorized individuals to:
- Enter restricted corporate offices
- Access server rooms
- Reach executive suites
- Remove hardware or sensitive equipment
- Install malicious devices
Unlike tailgating, badge cloning may not trigger immediate suspicion because the system registers valid access.
In high-security industries such as finance, data centers, healthcare, and energy infrastructure, this risk can have severe operational consequences.
Badge Cloning vs Tailgating
While both are physical access threats, they differ significantly:
Tailgating:
An unauthorized person follows an authorized individual into a restricted area without presenting credentials.
Badge Cloning:

An attacker duplicates a legitimate credential and gains independent access without assistance.
Both vulnerabilities are commonly identified during physical penetration testing engagements (link to your service page).
How Physical Penetration Testing Identifies Badge Cloning Risks
During authorized adversary simulation exercises, red team operators may:
- Attempt RFID credential capture
- Evaluate encryption strength of badge systems
- Test for unauthorized credential duplication
- Attempt entry using emulated credentials
- Assess detection and logging capabilities
These controlled tests help organizations understand whether their access control systems are vulnerable to credential replication attacks.
Learn more about enterprise physical red teaming services.
Common Vulnerabilities That Enable Badge Cloning
Badge cloning often occurs due to:
- Use of outdated low-frequency RFID systems
- Weak or absent encryption
- Lack of credential authentication layering
- No monitoring of unusual access patterns
- Poor revocation policies for lost badges
Organizations frequently assume access control systems are secure without validating encryption standards.
How to Prevent Badge Cloning Attacks
Enterprises can mitigate badge cloning risk by implementing:
1. Encrypted Smart Card Technology
Use modern high-frequency encrypted credential systems.
2. Multi-Factor Physical Authentication
Combine badge access with:
- PIN codes
- Biometrics
- Mobile authentication
3. Access Log Monitoring
Flag unusual access times or location patterns.
4. Regular Physical Penetration Testing
Simulated adversary testing validates real-world resilience.
5. Credential Lifecycle Management
Immediate revocation of lost or compromised badges.
Industries Most at Risk
Badge cloning poses elevated risk in environments such as:
- Data centers
- Financial institutions
- Healthcare facilities
- Manufacturing plants
- Critical infrastructure sites
Organizations operating globally — including the United States, Asia, and the GCC — often conduct recurring physical penetration testing to validate access control strength.
Related Physical Security Terms
- What Is Tailgating in Physical Security?
- What Is Physical Penetration Testing?
- Physical Access Control Systems Explained
- What Is Physical Red Teaming?
- What Is a Mantrap Security System?
- Attack Path Analysis in Red Teaming
- Controlled Intrusion Testing Explained
- What Is Threat Modeling in Physical Security?
What Is Badge Cloning? - Frequently Asked Questions
- How does badge cloning happen?Badge cloning occurs when an attacker captures data from a legitimate access credential and duplicates it onto another card or device to gain unauthorized entry.
- Are all access badges vulnerable to cloning?
No. Older low-frequency RFID badges are more vulnerable, while modern encrypted smart cards significantly reduce cloning risk.
- Can badge cloning be detected?Yes. Organizations can detect suspicious access patterns, duplicate credential usage, or unusual entry times through access log monitoring.
- How can organizations prevent badge cloning?
Prevention includes encrypted smart card technology, multi-factor authentication, strict badge management, and recurring physical penetration testing.

