A mantrap security system is a controlled physical access mechanism that uses a small enclosed space with two interlocking doors to regulate entry into a secure area. Only one door can open at a time, preventing unauthorized individuals from tailgating or entering restricted zones without proper authentication.
Mantrap systems are commonly deployed in high-security environments such as data centers, financial institutions, research facilities, and government buildings.
How a Mantrap Security System Works
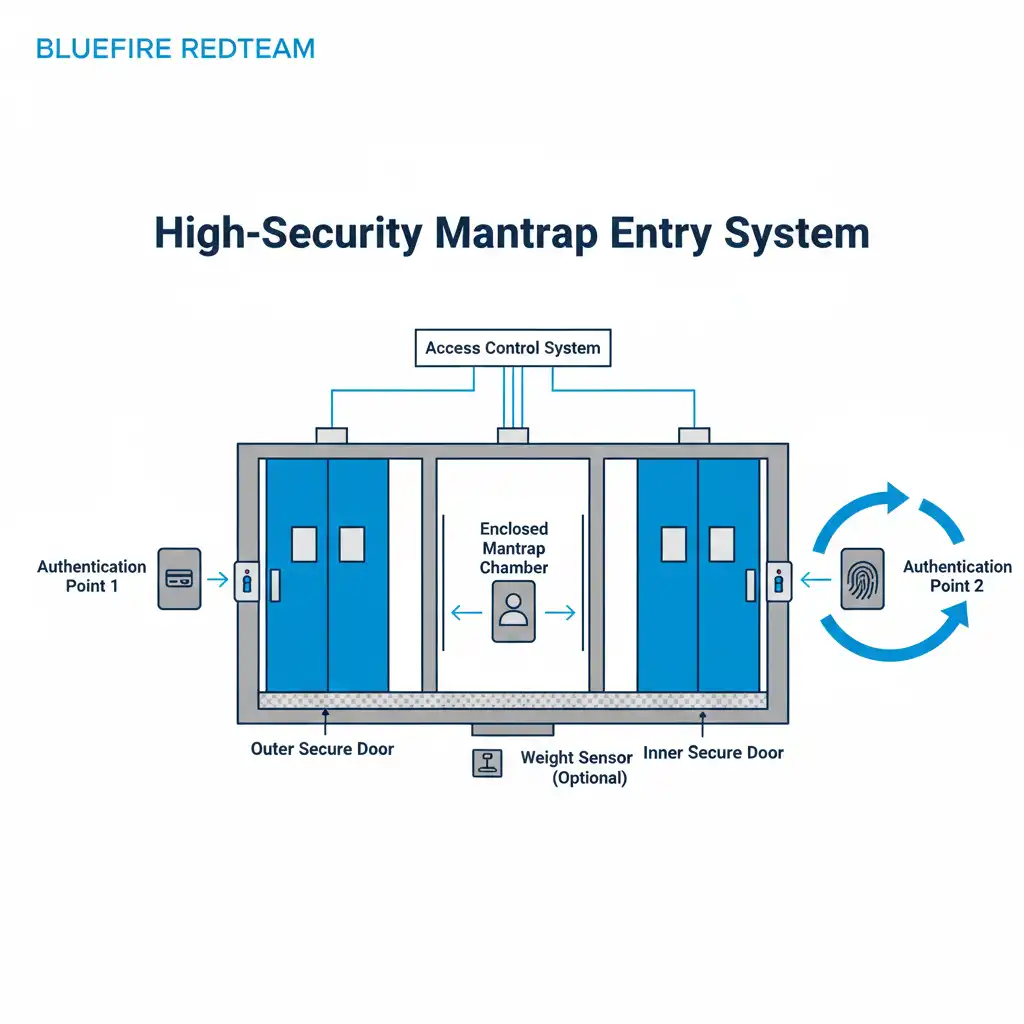
A mantrap consists of:
- Two sequential locking doors
- Authentication devices (badge reader, PIN pad, or biometrics)
- Access control software
- Surveillance integration
The typical process works as follows:
- An individual presents credentials at the first door.
- The first door unlocks and allows entry into the chamber.
- The first door closes and locks.
- The system verifies identity (sometimes requiring a second authentication factor).
- The second door unlocks if authorization is confirmed.
If authentication fails, both doors remain locked or the individual is directed to exit.
This controlled entry sequence prevents tailgating and unauthorized piggybacking.
Why Mantrap Security Systems Are Used
Mantraps provide enhanced protection in environments where:
- Sensitive data is stored
- Critical infrastructure is housed
- Regulatory compliance is required
- Insider threat risk must be mitigated
They are particularly common in:
- Data centers
- Financial institutions
- Healthcare facilities
- Research labs
- Government and defense facilities
In these environments, even a single unauthorized entry can have severe operational and regulatory consequences.
Mantrap Security Systems vs Standard Access Control

Standard badge-controlled doors allow entry when a credential is presented.
However, they may still be vulnerable to:
- Tailgating
- Social engineering
- Badge cloning
- Door propping
A mantrap adds an additional physical enforcement layer that prevents multiple individuals from entering simultaneously without verification.
This makes it significantly more resistant to common physical intrusion techniques.
Types of Mantrap Security Systems
There are several types of mantrap systems used in enterprise environments:
1. Basic Two-Door Mantrap
Requires credential authentication for entry and exit.
2. Biometric Mantrap
Uses fingerprint, facial recognition, or iris scanning for identity verification.
3. Weight-Sensing Mantrap
Includes floor sensors to detect more than one individual in the chamber.
4. Security Guard-Assisted Mantrap
Monitored in real time by security personnel who visually confirm identity before granting access.
High-security data centers often combine multiple authentication methods for layered protection.
Common Vulnerabilities in Mantrap Systems
Although mantraps significantly reduce risk, they are not immune to weaknesses.
Potential issues include:
- Poorly configured authentication settings
- Inconsistent enforcement of dual-factor authentication
- Tailgating into the first door
- Social engineering attempts before entry
- Misconfigured emergency override mechanisms
These vulnerabilities are frequently identified during physical penetration testing engagements.
How Physical Penetration Testing Evaluates Mantrap Security
During authorized adversary simulation exercises, security professionals may:
- Attempt dual-entry scenarios
- Test credential authentication strength
- Evaluate weight sensor calibration
- Assess guard monitoring attentiveness
- Attempt pretext-based bypass attempts
- Test emergency unlock procedures
Unlike a physical security audit, penetration testing validates whether the mantrap system functions effectively under realistic attack conditions.
Organizations seeking deeper validation often conduct comprehensive physical red team engagements to assess detection and response workflows.
Benefits of Implementing Mantrap Security Systems
Mantraps provide:
- Anti-tailgating protection
- Enhanced access accountability
- Multi-factor authentication enforcement
- Reduced insider threat exposure
- Regulatory compliance support
- Improved audit trail documentation
They are particularly effective when integrated into a layered physical security model.
Best Practices for Mantrap Implementation
Organizations should:
- Use encrypted smart card authentication
- Require multi-factor verification
- Regularly test sensor calibration
- Monitor access logs in real time
- Conduct recurring physical penetration testing
- Train employees on entry protocols
Technology alone does not eliminate risk; operational enforcement is critical.
Mantrap Systems in Data Centers
Data centers often require:
- Badge + biometric authentication
- Real-time surveillance integration
- 24/7 monitoring
- Access segmentation beyond the mantrap
The mantrap serves as a critical barrier before reaching server cages or network operations centers.
Learn more about data center physical security controls.
Mantrap Security and Insider Threat
Mantrap systems help mitigate insider threat by:
- Logging all entry attempts
- Preventing unauthorized accompaniment
- Restricting simultaneous access
- Supporting strict role-based permissions
When combined with strong access control policies, mantraps significantly increase physical resilience.
Related Physical Security Terms
- What Is Tailgating in Physical Security?
- Physical Access Control Systems Explained
- Data Center Physical Security Controls
- What Is Physical Penetration Testing?
- What Is Physical Red Teaming?
- Attack Path Analysis in Red Teaming
- Controlled Intrusion Testing Explained
- What Is Threat Modeling in Physical Security?

