RFID cloning is a physical security attack technique in which an attacker copies data from a radio frequency identification (RFID) access credential and transfers it to another device or blank card to gain unauthorized entry into a secured facility. It exploits weaknesses in low-frequency or improperly encrypted RFID systems and is a common vulnerability identified during physical penetration testing engagements.
RFID cloning allows attackers to replicate legitimate access badges without physical possession of the original credential.
What Is RFID Technology?
RFID (Radio Frequency Identification) is a wireless communication technology used to identify and authenticate objects or individuals via radio signals.
In physical access control systems, RFID is commonly used in:
- Employee access badges
- Proximity cards
- Smart cards
- Key fobs
An RFID system typically includes:
- A credential (badge or card)
- A reader device
- A backend access control panel
When a credential is presented near a reader, it transmits data that determines whether access is granted or denied.
How RFID Cloning Works
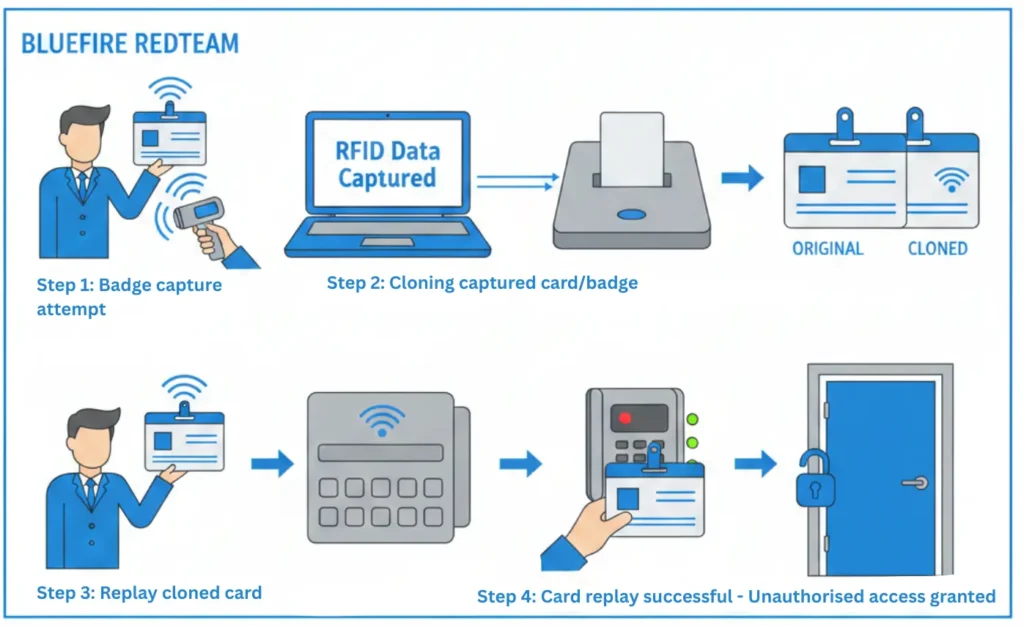
RFID cloning generally follows this process:
1. Credential Signal Capture
An attacker uses a handheld RFID scanner or concealed device to read data transmitted from a legitimate badge.
This can occur:
- In crowded environments
- Near office entrances
- In public transportation
- In shared workspaces
Low-frequency RFID cards (125 kHz) are especially vulnerable if unencrypted.
2. Data Extraction
The captured RFID data is transferred to a laptop or cloning tool.
3. Credential Duplication
The attacker writes the copied data onto:
- A blank RFID card
- A programmable key fob
- A mobile device capable of credential emulation
4. Unauthorized Access Attempt
The cloned credential is used at a facility entrance to bypass security controls.
If the system lacks encryption or anomaly detection, access may be granted without triggering alerts.
RFID-based systems are particularly vulnerable when outdated protocols are used. In a real-world assessment, attackers were able to extract keys and fully clone access credentials.
Read the RFID badge cloning case study
RFID Cloning vs Badge Cloning
The terms are related but slightly different.
RFID Cloning:
Specifically refers to duplicating credentials that use radio frequency identification technology.
Badge Cloning:
A broader term that may include RFID, magnetic stripe, or other credential technologies.
Most modern badge cloning risks involve RFID-based systems.
For more on this topic, see What Is Badge Cloning?
Why RFID Cloning Is a Serious Enterprise Risk
Unlike tailgating, RFID cloning does not rely on human behavior. It exploits technology weaknesses.
A successful cloned credential may allow attackers to:
- Enter restricted corporate offices
- Access data centers
- Reach executive areas
- Install malicious devices
- Remove sensitive equipment
Because the system registers the cloned credential as valid, detection may be delayed.
Organizations operating in financial services, healthcare, data centers, and energy infrastructure face elevated exposure.
Common RFID System Weaknesses

RFID cloning is often possible due to:
- Use of outdated low-frequency cards
- Lack of encryption
- Static credential identifiers
- No rolling authentication mechanisms
- Failure to monitor unusual access behavior
- Weak credential lifecycle management
Legacy systems are particularly vulnerable.
How Physical Penetration Testing Identifies RFID Cloning Risk
During authorized adversary simulation, security professionals may:
- Test RFID reader encryption strength
- Attempt controlled credential capture
- Evaluate cloning feasibility
- Attempt access using emulated credentials
- Assess access log monitoring capabilities
These tests validate whether access control systems can withstand real-world intrusion attempts.
Learn more about enterprise physical penetration testing services.
Advanced organizations also conduct physical red team engagements to evaluate detection and response processes.
How to Prevent RFID Cloning Attacks
Organizations can mitigate RFID cloning risk by implementing:
1. Encrypted Smart Card Technology
Upgrade from low-frequency (125 kHz) cards to high-frequency encrypted smart cards.
2. Mutual Authentication Protocols
Use credentials that verify both card and reader authenticity.
3. Multi-Factor Authentication
Combine badge access with:
- PIN codes
- Biometrics
- Mobile verification
4. Access Behavior Monitoring
Identify unusual access times or abnormal movement patterns.
5. Regular Physical Penetration Testing
Simulated adversary testing ensures technical controls function under pressure.
Industries Most Vulnerable to RFID Cloning
RFID cloning risk is especially significant in:
- Data centers
- Financial institutions
- Healthcare facilities
- Manufacturing environments
- Corporate headquarters
- Critical infrastructure sites
Global enterprises across the United States, Asia, and the GCC increasingly integrate RFID security validation into their facility risk management programs.
RFID Cloning and Compliance
In regulated industries, compromised access control systems can result in:
- Regulatory penalties
- Compliance violations
- Audit failures
- Loss of customer trust
Access control validation should be part of a comprehensive security strategy.
Related Physical Security Terms
- What Is Badge Cloning?
- What Is Physical Access Control Systems?
- What Is Physical Penetration Testing?
- What Is Tailgating in Physical Security?
- What Is a Mantrap Security System?
- Attack Path Analysis in Red Teaming
- Controlled Intrusion Testing Explained
- What Is Threat Modeling in Physical Security?
RFID Cloning Explained - Frequently Asked Questions
- What is the difference between RFID cloning and badge cloning?RFID cloning specifically refers to duplicating radio frequency credentials, while badge cloning may include other credential technologies.
- Are high-frequency RFID cards secure?High-frequency encrypted smart cards are significantly more secure than older low-frequency systems, but proper configuration is essential.
- Can mobile devices be used for RFID cloning?In some cases, attackers may use programmable devices to emulate RFID credentials if systems lack strong encryption.
- How do organizations reduce RFID cloning risk?Risk reduction includes encrypted smart cards, multi-factor authentication, strict access reviews, and recurring security testing.

