A real-world physical security assessment revealed how a widely used RFID-based access control system could be fully compromised using badge cloning techniques.
In this case study, we demonstrate how an attacker can bypass access controls, clone employee credentials, and gain unauthorized access to restricted areas using commercially available tools.
Overview of the Security Assessment
A mid-sized enterprise engaged Bluefire Redteam to evaluate the effectiveness of its RFID-based access control system across corporate facilities.
Objective:
Determine whether an attacker could gain unauthorized access by cloning employee RFID badges.
Scope of Testing
The engagement included:
- RFID-based access control systems
- Employee access badges
- Entry gates and internal office areas
- Restricted zones and sensitive access points
Testing was conducted using a black-box approach, simulating a real-world attacker with no prior knowledge.
Attack Methodology
The assessment followed a structured offensive approach:
- RFID reconnaissance
- Chip identification and protocol analysis
- Cryptographic weakness exploitation
- Badge cloning and emulation
- Real-world access validation
Phase 1: RFID Reconnaissance
Using industry-standard tools, the team identified the badge technology:
- Card Type: MIFARE Classic 1K
- Weak proprietary encryption (Crypto1)
- Known vulnerabilities in authentication mechanisms
Key Insight:
This card type is widely used but cryptographically broken, making it vulnerable to cloning attacks.
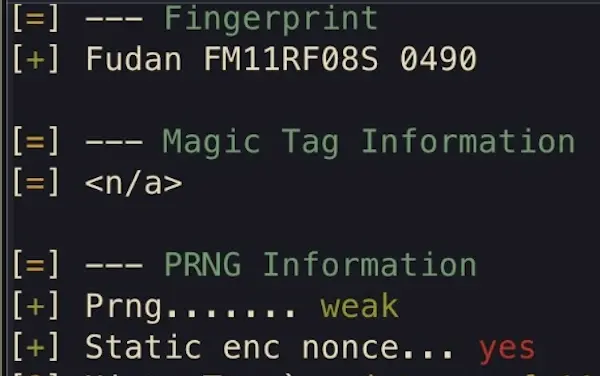
Phase 2: Weakness Identification
Further analysis revealed:
- Predictable random number generation
- Reusable authentication values
- No secure cryptographic implementation
Security Risk:
These weaknesses allow attackers to recover encryption keys and replicate the card.
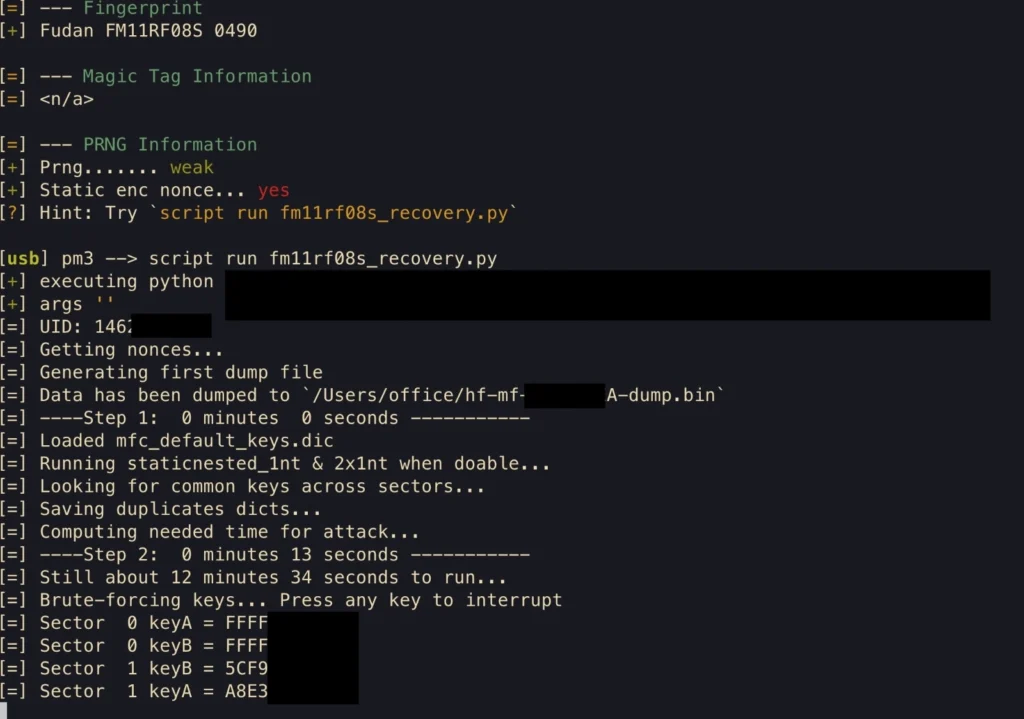
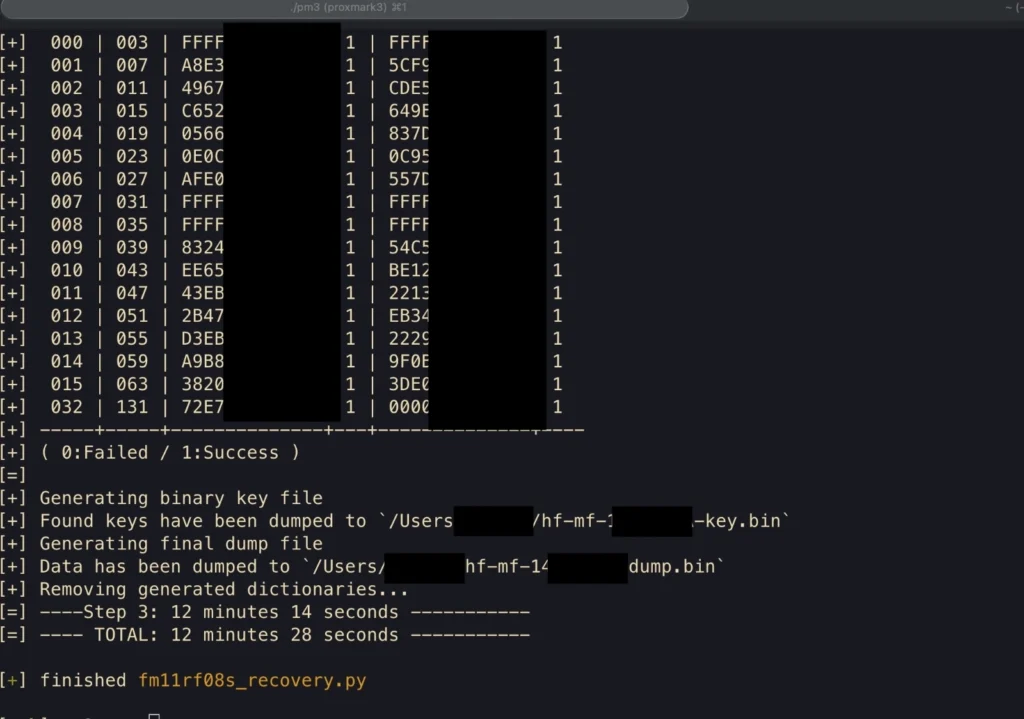
Phase 3: Key Extraction and Badge Cloning
Using specialized tools, all encryption keys were recovered.
Result:
- Full badge memory extracted
- All access credentials replicated
- No protection against duplication
👉 This enabled the complete cloning of legitimate employee badges
Phase 4: Badge Emulation
The cloned badge was emulated using hardware tools.
Outcome:
- Identical behavior to original badge
- Full access replication
- No detection by access control system
Phase 5: Access Control Bypass
The cloned badge was tested across multiple access points:
- Entry gates
- Office floors
- Restricted zones
Results:
- ✅ Unauthorized access granted
- ❌ No anomaly detection
- ❌ No duplicate credential alerts
- ❌ No backend validation
Advanced Attack Scenarios
Additional testing revealed:
UID-Only Attack
- Partial access granted in some areas
Duplicate Badge Usage
- Original + cloned badge used simultaneously
- No anti-passback enforcement
Critical Security Findings
Full Badge Cloning Was Possible
All sectors and credentials were successfully replicated.
Broken Cryptography
The system relied on outdated encryption vulnerable to known attacks.
No Backend Validation
Access decisions were based solely on badge data without verification.
Weak Key Management
Default keys were still in use across multiple sectors.
Business Impact
This vulnerability allowed:
- Unauthorized facility access
- Employee impersonation
- Lateral movement within the organization
- Potential data and infrastructure compromise
A single compromised badge enabled full facility access replication
Root Cause Analysis
The compromise was caused by:
- Use of insecure RFID technology
- Lack of encryption upgrades
- Poor credential management
- Absence of anomaly detection
Security Recommendations
Immediate Actions
- Replace legacy cards with secure alternatives (e.g., DESFire EV2)
Medium-Term Improvements
- Implement backend authentication
- Enable anti-passback controls
- Monitor duplicate badge usage
Long-Term Strategy
- Upgrade communication protocols
- Encrypt reader-to-controller communication
- Conduct regular physical penetration testing
Key Takeaway
Physical security systems are only as strong as their weakest component.
In this case, a single badge vulnerability enabled complete system compromise.
Test Your Physical Security Before an Attacker Does
Most organizations assume their access control systems are secure until they are tested under real-world conditions.
This case study demonstrates how easily modern attackers can bypass physical defenses using practical techniques.
Don’t wait for a real breach.
- Identify vulnerabilities in your access control systems
- Test real-world attack scenarios
- Validate detection and response capabilities


