Data center physical security controls are the layered safeguards implemented to prevent unauthorized physical access to critical IT infrastructure, servers, and networking equipment. These controls are designed to protect sensitive data, ensure operational continuity, and mitigate risks such as theft, sabotage, insider compromise, and hardware tampering.
Because data centers store mission-critical systems and confidential information, physical security is considered as important as cybersecurity controls.
Why Data Center Physical Security Matters
Data centers host:
- Customer data
- Financial records
- Intellectual property
- Cloud infrastructure
- Critical business systems
- Government or regulated workloads
A single physical breach can result in:
- Data exfiltration
- Network compromise
- Hardware implantation attacks
- Regulatory violations
- Business disruption
Unlike general office environments, data centers require enhanced physical protection due to the concentration of sensitive infrastructure.
Core Layers of Data Center Physical Security
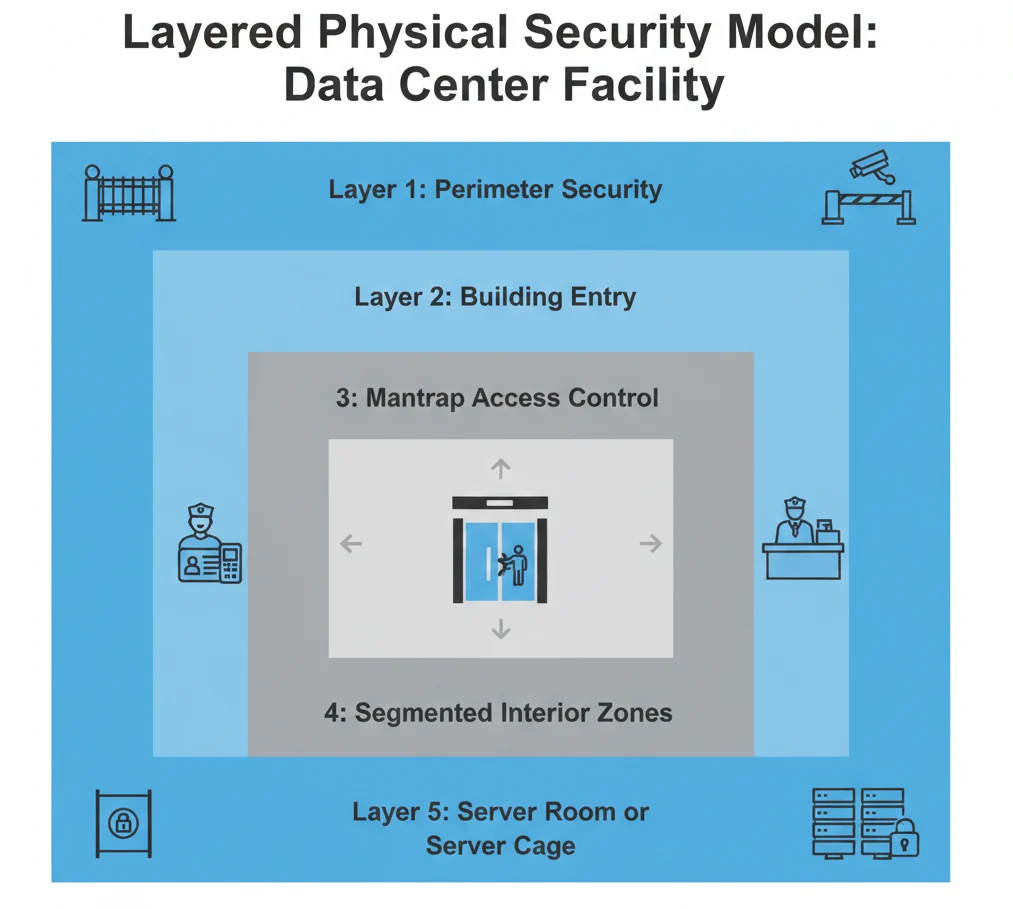
Modern data centers implement a layered security model to reduce risk exposure.
1. Perimeter Security
The outermost defense layer includes:
- Fencing and controlled vehicle access
- Bollards and crash barriers
- Security patrols
- Exterior surveillance cameras
- Controlled parking access
Perimeter controls are designed to deter unauthorized entry before reaching the facility itself.
2. Building Access Control
Entry into the facility typically requires:
- Multi-factor authentication (badge + PIN or biometrics)
- Mantrap security systems
- Guard verification procedures
- Visitor pre-registration
- Strict escort policies
Many high-security data centers use two-factor or three-factor authentication to prevent unauthorized access.
3. Interior Access Segmentation
Within the facility, additional controls restrict access to sensitive zones:
- Server rooms
- Network operations centers (NOC)
- Power distribution areas
- Backup storage rooms
Access is typically role-based and logged in real time.
Learn more about physical access control systems
4. Surveillance and Monitoring
Continuous monitoring includes:
- 24/7 CCTV coverage
- Motion detection systems
- Access log auditing
- Security operations center oversight
Surveillance systems must be actively monitored, not just recorded.
5. Environmental Controls
While not always categorized as traditional “security,” environmental controls protect infrastructure integrity:
- Temperature regulation systems
- Fire suppression systems
- Water leak detection
- Power redundancy
Physical security extends beyond intrusion prevention to infrastructure resilience.
Common Data Center Physical Vulnerabilities
Even high-security facilities may contain weaknesses, including:
- Weak visitor credential enforcement
- Badge sharing between contractors
- Inadequate escort policies
- Poor access log review
- Unsecured equipment racks
- Insufficient server cage protection
- Overly broad employee access privileges
These vulnerabilities are frequently identified during physical penetration testing engagements.
How Physical Penetration Testing Evaluates Data Center Controls

During authorized adversary simulation exercises, red team operators may:
- Attempt controlled entry using social engineering
- Test badge authentication enforcement
- Evaluate mantrap procedures
- Assess after-hours access policies
- Validate CCTV monitoring responsiveness
- Test hardware removal detection
Unlike audits, penetration tests assess whether security controls function under realistic attack scenarios.
Organizations operating global data centers across the United States, Asia, and the GCC increasingly integrate physical red teaming into their risk management strategy.
Learn more about physical red team engagements.
Compliance and Regulatory Considerations
Data centers often fall under regulatory frameworks such as:
- Financial industry regulations
- Healthcare compliance requirements
- Data protection standards
- Government security mandates
Physical access control failures can result in:
- Compliance violations
- Financial penalties
- Loss of certifications
- Customer trust erosion
Regular physical security validation is critical for maintaining regulatory posture.
Data Center Security vs Standard Office Security
Data center physical security differs from standard office environments in several ways:
| Feature | Standard Office | Data Center |
|---|---|---|
| Authentication | Badge only | Multi-factor authentication |
| Monitoring | Limited CCTV | 24/7 monitored surveillance |
| Visitor Access | Reception-based | Pre-approved and escorted |
| Access Segmentation | Limited | Highly restricted zones |
| Logging | Basic access logs | Real-time auditing and review |
The increased concentration of sensitive systems requires stricter enforcement and layered protection.
Best Practices for Strengthening Data Center Physical Security
Organizations can enhance resilience by:
- Implementing encrypted smart card technology
- Enforcing strict visitor management policies
- Using mantrap entry systems
- Conducting regular access reviews
- Monitoring access logs in real time
- Performing recurring physical penetration testing
Periodic testing ensures controls remain effective as infrastructure evolves.
Insider Threat in Data Centers
Data centers are particularly vulnerable to insider threats because authorized personnel may have elevated access privileges.
Risk mitigation includes:
- Role-based access restrictions
- Segregation of duties
- Continuous monitoring
- Behavioral anomaly detection
- Background screening policies
Red team simulations often include insider threat scenarios to evaluate resilience.
The Role of Physical Red Teaming in Data Centers
Physical red team engagements provide:
- Real-world adversary simulation
- Detection and response testing
- Executive-level risk visibility
- Operational security validation
For organizations with high-value infrastructure, physical red teaming is increasingly considered a strategic necessity rather than an optional assessment.
Related Physical Security Terms
- What Is Physical Penetration Testing?
- Physical Access Control Systems Explained
- What Is Social Engineering in Physical Security?
- What Is RFID Cloning?
- What Is a Mantrap Security System?
- Attack Path Analysis in Red Teaming
- Controlled Intrusion Testing Explained
- What Is Threat Modeling in Physical Security?
Data Center Physical Security Controls - FAQ
- What physical security controls are required in a data center?Data centers typically require layered controls including perimeter security, multi-factor access authentication, mantrap systems, surveillance monitoring, and restricted zone segmentation.
- Are mantrap systems mandatory in data centers?Mantrap systems are not universally mandatory, but they are widely implemented in high-security data centers to prevent tailgating and enforce multi-factor authentication.
- How often should data centers test physical security?Mantrap systems are not universally mandatory, but they are widely implemented in high-security data centers to prevent tailgating and enforce multi-factor authentication.
- What is the biggest physical risk to data centers?Common risks include unauthorized access, insider credential misuse, hardware tampering, and failure to detect intrusion attempts.

