Controlled intrusion testing is a structured and authorized physical security assessment in which security professionals simulate real-world intrusion attempts under defined rules of engagement. The objective is to identify exploitable vulnerabilities in facility defenses while maintaining operational safety and legal compliance.
Unlike unauthorized intrusion, controlled intrusion testing is conducted with executive approval, documented scope boundaries, and predefined escalation protocols.
It is commonly used by enterprise organizations seeking to validate the effectiveness of physical security controls without introducing uncontrolled operational risk.
What Is Controlled Intrusion Testing?
Controlled intrusion testing is a subset of physical penetration testing that focuses specifically on simulating unauthorized physical access attempts in a controlled environment.
The term emphasizes:
- Formal authorization
- Safety oversight
- Defined testing boundaries
- Clear engagement scope
- Coordinated communication protocols
Organizations often prefer this terminology when engaging board members or regulatory stakeholders.
How Controlled Intrusion Testing Works
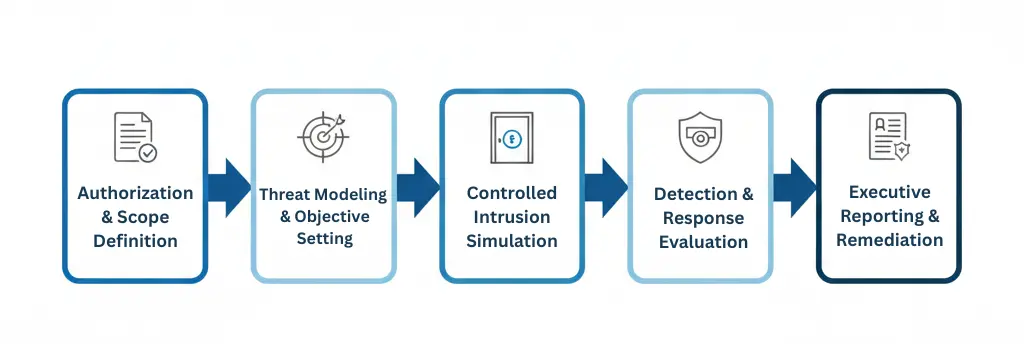
A typical engagement follows a structured methodology:
1. Authorization and Scope Definition
Before testing begins, the organization defines:
- Facilities in scope
- Areas restricted from testing
- Allowed techniques
- Time windows
- Safety constraints
Formal written authorization is mandatory.
2. Threat Modeling and Objective Setting
Security teams define target objectives, such as:
- Accessing a restricted server room
- Entering a data center cage
- Testing after-hours access enforcement
- Evaluating tailgating resistance
Objectives align with realistic adversary scenarios.
3. Controlled Intrusion Attempts
Authorized operators simulate intrusion techniques including:
- Social engineering
- Tailgating
- Badge misuse
- Credential cloning feasibility
- Mantrap enforcement testing
- Escort policy evaluation
All actions remain within predefined legal and operational boundaries.
4. Detection and Response Evaluation
Controlled intrusion testing assesses not only prevention, but also:
- Surveillance monitoring
- Guard response times
- Escalation procedures
- Incident reporting accuracy
This provides a complete view of organizational resilience.
5. Executive Reporting
Findings are documented in a structured report that includes:
- Exploited vulnerabilities
- Attack path analysis
- Evidence and timelines
- Risk impact assessment
- Remediation recommendations
This allows leadership to prioritize corrective actions.
Controlled Intrusion Testing vs Physical Security Audits
A physical security audit evaluates whether policies and procedures are documented and implemented.
Controlled intrusion testing evaluates whether those controls prevent real-world intrusion.
Audits focus on compliance.
Controlled intrusion testing focuses on operational effectiveness.
Organizations often use both approaches for comprehensive risk visibility.
Controlled Intrusion Testing vs Physical Red Teaming
While related, these methodologies differ in scope.
Controlled Intrusion Testing:
- Focused on facility access validation
- Structured and scoped
- May test specific objectives
Physical Red Teaming:
- Broader adversary simulation
- May include multi-layer attack paths
- Tests detection, response, and escalation
- Often includes insider threat scenarios
Learn more about enterprise physical red team engagements.
Why Enterprises Use Controlled Intrusion Testing

Organizations conduct controlled intrusion testing to:
- Validate physical access control systems
- Identify behavioral security gaps
- Test mantrap enforcement
- Evaluate data center security
- Measure guard effectiveness
- Reduce regulatory risk exposure
Enterprises operating across the United States, Asia, and the GCC increasingly adopt recurring intrusion validation as part of security maturity programs.
Common Vulnerabilities Identified During Testing
Controlled intrusion testing often reveals:
- Weak badge enforcement
- Unchallenged unknown individuals
- Poor visitor management practices
- Inadequate access log review
- Unsecured restricted areas
- Lax after-hours monitoring
These vulnerabilities may not be visible during checklist-based assessments.
Controlled Intrusion Testing in Data Centers
High-security facilities such as data centers commonly use controlled intrusion testing to evaluate:
- Perimeter enforcement
- Mantrap authentication strength
- Server cage access segmentation
- Contractor escort compliance
- Hardware removal detection
Learn more about data center physical security controls.
Risk Mitigation Through Recurring Testing
Security controls degrade over time due to:
- Employee turnover
- Complacency
- System misconfiguration
- Policy drift
Recurring controlled intrusion testing ensures defenses remain effective as environments evolve.
This testing model is often part of comprehensive physical penetration testing services.
Controlled Intrusion Testing and Insider Threat
Insider threat risk can also be evaluated through structured intrusion testing.
Scenarios may include:
- Credential misuse
- Unauthorized zone access
- Shared badge testing
- Privilege abuse
When properly scoped, these scenarios provide valuable risk insight without operational disruption.
Best Practices for Controlled Intrusion Testing
Organizations should:
- Obtain executive-level authorization
- Define clear rules of engagement
- Establish emergency stop procedures
- Coordinate with legal and compliance teams
- Protect employee privacy
- Conduct post-engagement debriefs
Professional oversight ensures testing enhances security rather than introducing risk.

