Attack path analysis in red teaming is the systematic process of identifying, mapping, and evaluating the sequence of steps an adversary could take to achieve a specific objective within a target environment. In physical security contexts, attack path analysis examines how layered security controls might be bypassed through a combination of technical, procedural, and human vulnerabilities.
Rather than testing isolated weaknesses, attack path analysis focuses on how multiple small vulnerabilities can be chained together to produce a successful intrusion.
What Is an Attack Path?
An attack path is a logical sequence of actions that a threat actor could follow to reach a defined target, such as:
- Accessing a restricted server room
- Reaching executive offices
- Removing sensitive hardware
- Gaining after-hours facility entry
- Implanting unauthorized devices
Each step in the path exploits a weakness, whether technical, procedural, or behavioral.
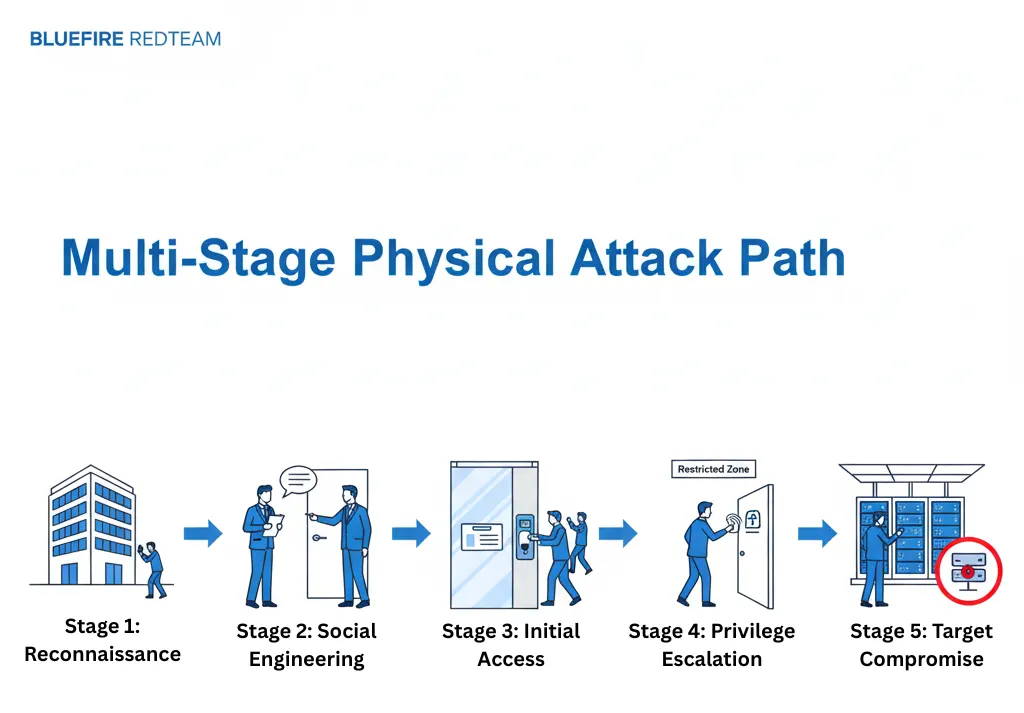
Attack paths are rarely single-step events – they are multi-stage processes.
Why Attack Path Analysis Matters in Physical Red Teaming
In many organizations, individual controls may appear secure when evaluated independently.
However, risk emerges when:
- Badge access is strong
- But tailgating is common
- Surveillance exists
- But is not actively monitored
- Guards are present
- But escalation procedures are weak
Attack path analysis reveals how these weaknesses combine.
This methodology is central to advanced physical red team engagements.
The Core Components of Attack Path Analysis
Effective attack path analysis typically involves:
1. Objective Definition
Identify the end goal of the adversary.
Examples:
- Gain server rack access
- Reach restricted data center cage
- Bypass mantrap entry
- Access executive suite
2. Threat Modeling
Define potential attacker profiles:
- External opportunistic intruder
- Organized adversary
- Insider collaborator
- Social engineering specialist
Each profile has different capabilities and motivations.
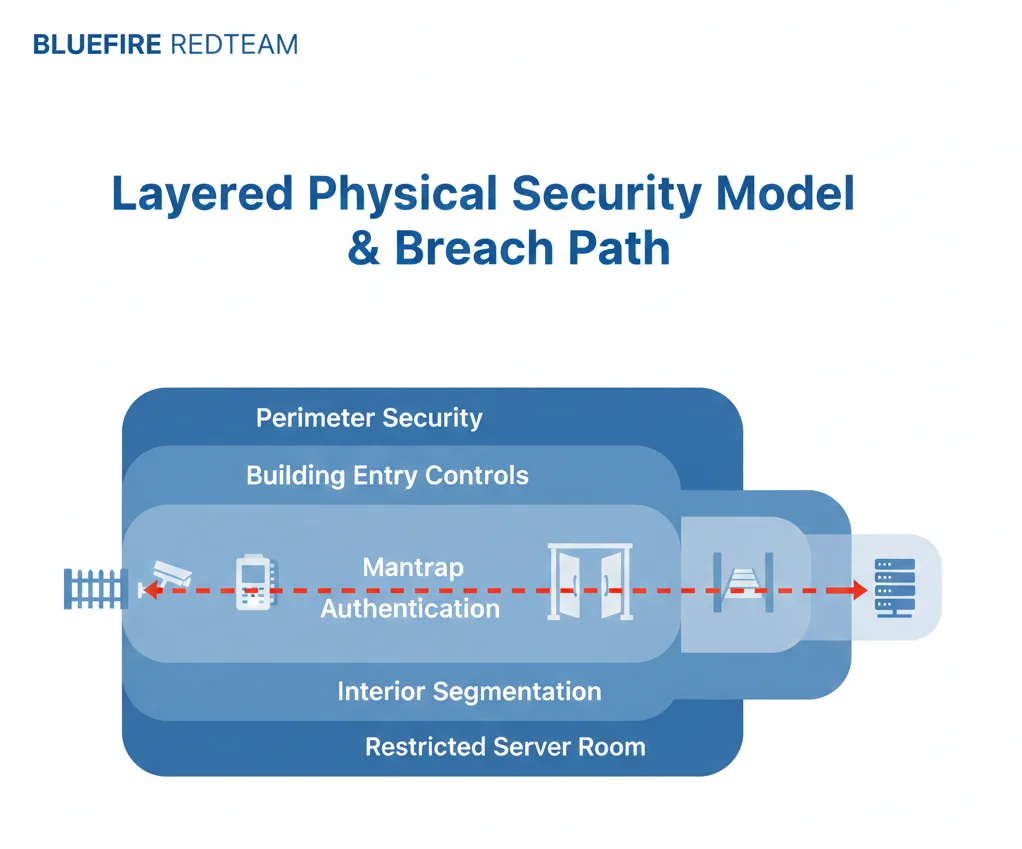
3. Control Mapping
Document all existing physical security controls:
- Perimeter fencing
- Badge access systems
- Biometric authentication
- Surveillance cameras
- Guard patrols
- Visitor management policies
This creates a baseline of defensive layers.
4. Vulnerability Identification
Identify potential weaknesses in each layer, including:
- Unencrypted RFID credentials
- Lax badge enforcement
- Unchallenged visitors
- Weak escort procedures
- Poor access log monitoring
5. Path Construction
Map how vulnerabilities can be chained together.
Example physical attack path:
- Reconnaissance of employee routines
- Social engineering entry into lobby
- Tailgating through badge-controlled door
- Use of cloned credential for restricted zone
- Entry into server cage
- Removal of hardware
Each step alone may seem minor. Together, they create breach potential.
Attack Path Analysis vs Vulnerability Scanning
Traditional vulnerability scanning identifies isolated weaknesses.
Attack path analysis identifies exploit sequences.
This distinction is critical.
A facility may have 10 minor vulnerabilities that appear low risk independently, but when combined, they create a viable intrusion route.
This is why organizations conducting physical penetration testing services often prioritize attack path mapping.
Real-World Examples of Physical Attack Paths
Example 1: Data Center Breach Path
- Public reconnaissance
- Contractor impersonation
- Tailgating through main entrance
- Access to unsecured staging area
- Lateral movement to restricted cage
- Equipment removal
Example 2: Executive Office Access
- Social engineering receptionist
- Badge override request
- Elevator access exploitation
- After-hours access abuse
These scenarios illustrate how human and technical weaknesses combine.
How Red Teams Use Attack Path Analysis
Professional red teams use attack path analysis to:
- Prioritize testing objectives
- Simulate realistic adversary behavior
- Evaluate multi-layer defense effectiveness
- Test detection and response workflows
- Provide executive-level risk visibility
Rather than “trying random attacks,” red teams follow structured adversary logic.
This approach provides actionable insight instead of checklist findings.
The Role of Insider Threat in Attack Paths
Insiders dramatically alter attack path complexity.
An insider may:
- Provide credential access
- Disable monitoring temporarily
- Share restricted zone access
- Circumvent multi-factor authentication
Attack path analysis must account for both external and insider scenarios.
How Organizations Strengthen Against Attack Paths
Mitigation requires:
Layered Security
Multiple overlapping controls to prevent single-point failure.
Detection & Response Integration
Security teams must respond to anomalies in real time.
Access Segmentation
Limit lateral movement opportunities.
Strict Credential Management
Prevent badge cloning and unauthorized duplication.
Recurring Physical Penetration Testing
Validate that controls disrupt realistic attack sequences.
Organizations operating across the United States, Asia, and the GCC increasingly adopt structured red team methodologies to test attack paths comprehensively.
Attack Path Analysis and Executive Risk Reporting
Attack path analysis is particularly valuable for executive leadership because it:
- Translates technical findings into narrative risk scenarios
- Demonstrates real-world impact
- Quantifies likelihood and consequence
- Supports strategic security investment decisions
Rather than presenting isolated vulnerabilities, attack path reporting presents a clear story:
“This is how an attacker could reach your most critical assets.”
Attack Path Analysis in Data Centers
In high-security environments such as data centers, attack path analysis may include:
- Perimeter access evaluation
- Mantrap authentication bypass attempts
- Badge cloning feasibility
- Escort enforcement weaknesses
- Server cage segmentation testing
These layered evaluations reveal true resilience.
Learn more about data center physical security controls.

