Threat modeling in physical security is the structured process of identifying potential adversaries, defining their objectives, assessing their capabilities, and analyzing how they could exploit vulnerabilities within a physical environment. It is used to prioritize security controls based on realistic attack scenarios rather than theoretical risks.
In enterprise environments, threat modeling enables organizations to align physical security investments with actual risk exposure.
What Is Threat Modeling?
Threat modeling is a proactive risk assessment methodology that answers four critical questions:
- Who could target the organization?
- What are they trying to achieve?
- How could they accomplish it?
- What controls would prevent or detect the attack?
In physical security contexts, this process evaluates how adversaries could gain unauthorized access to facilities, sensitive infrastructure, or restricted areas.
Threat modeling shifts security from reactive control implementation to strategic risk planning.
Why Threat Modeling Is Critical in Physical Security
Many organizations deploy physical security controls without clearly understanding their threat landscape.
For example:
- A corporate office may implement badge access systems.
- A data center may deploy mantrap entry controls.
- Surveillance cameras may be installed across facilities.
However, without threat modeling, organizations may not know:
- Which assets are most likely to be targeted
- Which attacker types pose the greatest risk
- Which controls provide the highest return on investment
Threat modeling ensures security resources are allocated based on realistic adversary scenarios.
Key Components of Physical Threat Modeling

Effective physical threat modeling includes several structured steps.
1. Asset Identification
Define what must be protected.
Examples include:
- Data center infrastructure
- Executive offices
- Sensitive documents
- Intellectual property
- Restricted research areas
- Hardware storage facilities
Assets should be ranked by criticality and impact.
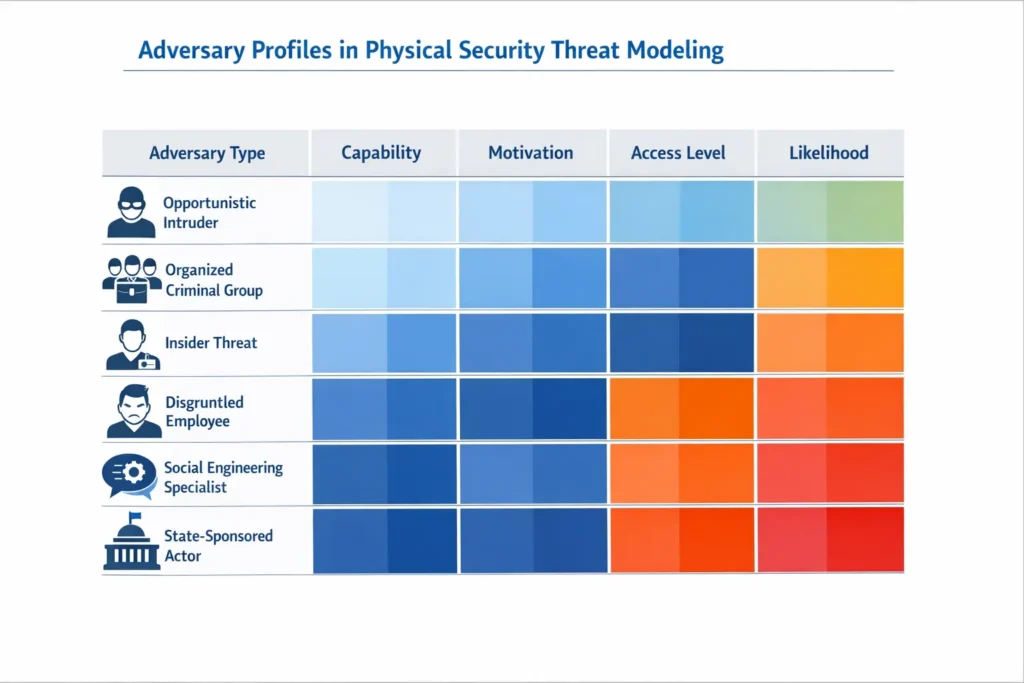
2. Adversary Profiling
Identify potential threat actors, such as:
- Opportunistic intruders
- Organized criminal groups
- Insider threats
- Disgruntled employees
- Social engineering specialists
- State-sponsored actors
Each adversary type has different motivations and capabilities.
3. Objective Definition
Define what adversaries might attempt to accomplish:
- Facility entry
- Server rack access
- Hardware theft
- Surveillance disruption
- Credential misuse
- Executive targeting
Clear objective definition allows structured risk analysis.
4. Vulnerability Mapping
Document weaknesses across security layers, including:
- Perimeter controls
- Badge authentication systems
- Mantrap enforcement
- Escort policies
- Surveillance monitoring
- Access log review procedures
This stage identifies exploitable gaps.
5. Attack Path Development
Using the identified vulnerabilities, construct possible intrusion scenarios.
For example:
- Social engineering entry at reception
- Tailgating into restricted corridor
- Credential cloning to bypass secondary controls
- Access to server cage
This stage overlaps closely with attack path analysis in red teaming.
Threat Modeling vs Physical Security Audits
A physical security audit evaluates whether policies exist and are documented.
Threat modeling evaluates whether controls address realistic adversary behavior.
Audits focus on compliance.
Threat modeling focuses on strategic risk anticipation.
Organizations that rely solely on audits may overlook emerging threat patterns.
Threat Modeling vs Physical Penetration Testing
Threat modeling is predictive.
Physical penetration testing is operational.
Threat modeling asks:
“What could happen?”
Penetration testing asks:
“Does it actually work?”
Together, they create a comprehensive physical security validation strategy.
Learn more about physical penetration testing services.
How Threat Modeling Supports Physical Red Teaming

Threat modeling informs the scope and objectives of advanced physical red team engagements.
Instead of random testing, red teams simulate:
- High-probability adversary behavior
- High-impact attack paths
- Insider threat scenarios
- Data center targeting strategies
Threat modeling ensures testing aligns with real-world risk.
Threat Modeling in Data Centers
Data centers require structured threat modeling because they:
- Concentrate critical assets
- Support cloud infrastructure
- Host regulated data
- Operate continuously
Threat modeling in data centers may consider:
- External intrusion attempts
- Contractor misuse
- Insider credential abuse
- After-hours exploitation
- Multi-layer authentication bypass
Learn more about data center physical security controls (link to that glossary post).
Benefits of Threat Modeling in Physical Security
Organizations that implement threat modeling benefit from:
- Prioritized security investments
- Reduced redundant controls
- Improved executive risk communication
- Better red team alignment
- Enhanced regulatory readiness
- Stronger layered defense strategy
Threat modeling enables leadership to see physical security as risk management – not just infrastructure expense.
Common Mistakes in Physical Threat Modeling
Organizations often:
- Assume low likelihood without analysis
- Overestimate control effectiveness
- Ignore insider threat risk
- Fail to update threat models regularly
- Separate physical and cybersecurity threat planning
Modern adversaries frequently blend physical and digital tactics.
Threat modeling should account for hybrid attack scenarios.
Best Practices for Effective Physical Threat Modeling
- Conduct recurring threat assessments
- Include cross-functional stakeholders
- Integrate insider threat scenarios
- Map realistic attack paths
- Validate assumptions with physical penetration testing
- Update models after major operational changes
Threat modeling is not a one-time exercise – it evolves with the organization.
Executive Value of Threat Modeling
For executive leadership, threat modeling:
- Translates physical security into business risk
- Clarifies impact and likelihood
- Supports strategic investment decisions
- Strengthens board-level reporting
Rather than presenting isolated vulnerabilities, threat modeling presents structured risk narratives.

