Cloud environments are not “secure by default.”
As businesses move more workloads into AWS, Azure, and Google Cloud, attackers increasingly target cloud identity systems, serverless functions, misconfigured storage, vulnerable APIs, and over-privileged IAM roles.
And here’s the truth:
Most cloud breaches happen despite having CSPM tools, compliance scans, or basic cloud security checklists.
Real attackers don’t follow checklists.
They exploit:
- IAM privilege escalation paths
- Publicly exposed storage buckets
- Misconfigured APIs
- Weak cross-account trust policies
- Cloud metadata abuse (SSRF → token theft)
- Lateral movement across cloud services
This is why cloud penetration testing — real offensive security, not automated scanning — is now essential.
This guide will show you:
- What cloud pen testing includes
- What AWS/Azure/GCP allow and restrict
- The methodology real attackers use
- The true cost of a cloud pen test
- How to evaluate cloud testing providers
- Why Bluefire’s offensive approach delivers deeper findings
If you’re a CISO, Cloud Architect, or Security Lead preparing for a cloud pen test, this guide is your blueprint.
What Is Cloud Penetration Testing? (Simple Definition)

Cloud penetration testing is a human-led offensive security assessment that simulates real-world attacks against AWS, Azure, or GCP environments to identify exploitable attack paths, privilege escalation routes, and data exposure risks.
Unlike vulnerability scans or CSPM tools, cloud pentesting:
- Exploits misconfigurations
- Chains weaknesses into real attack paths
- Simulates identity compromise
- Validates business impact
- Tests lateral movement across services
- Demonstrates real breach scenarios
The goal is not to find theoretical issues.
The goal is to answer:
“If an attacker gained access today — how far could they go?”
Why Cloud Penetration Testing Is Now a CISO Priority
Security frameworks from organizations like NIST and OWASP emphasize adversarial validation — not just configuration audits.
Cloud environments are dynamic:
- New services deployed daily
- CI/CD pipelines pushing changes
- IAM roles constantly evolving
- Multi-account and hybrid architectures
- DevOps-driven deployments
Static tools cannot keep up with real attacker behavior.
Cloud penetration testing provides:
- Real attack validation
- Identity risk exposure mapping
- Cross-service pivot simulation
- Evidence-based remediation guidance
- Compliance support (SOC 2, ISO 27001, PCI DSS, HIPAA)
What Cloud Penetration Testing Includes
1. Cloud Reconnaissance & Attack Surface Mapping
Security teams begin by identifying:
- IAM roles and policies
- Trust relationships
- Public-facing assets
- API endpoints
- VPC architecture
- Cross-account access
- Cloud-native services in use
This builds a complete map of your cloud attack surface.
2. IAM Privilege Escalation Testing
Identity is the #1 cloud attack vector.
Cloud pentesting simulates:
- Role chaining
- Temporary credential abuse
- Token theft via metadata
- Cross-service privilege escalation
- Dormant admin path discovery
- Trust policy abuse
This phase often reveals how low-level access can escalate to full administrator privileges.
3. Misconfiguration Exploitation
Testing includes:
- Public S3 / Blob / Cloud Storage exposure
- Overly permissive security groups
- API Gateway misconfiguration
- Serverless function weaknesses
- Weak secret storage
- Insecure cloud metadata handling
This is where most real-world cloud breaches originate.
4. Lateral Movement Across Cloud Services
Real attackers rarely stop at initial access.
Cloud penetration testing simulates movement such as:
- EC2 → RDS
- Lambda → DynamoDB
- Azure VM → Key Vault
- GCP Compute → Cloud Storage
- IAM → Log tampering
- Cloud → On-prem hybrid pivot
This determines how deeply an attacker could compromise your environment.
5. Data Exfiltration & Persistence Testing
Security teams validate:
- Whether sensitive data can leave undetected
- If logging captures attacker activity
- If DLP solutions block exploit traffic
- Whether persistence mechanisms can be established
This assesses true business risk — not theoretical risk.
Cloud Pen Testing vs Cloud Security Audits
| Cloud Security Audit | Cloud Penetration Test |
|---|---|
| Checklist-driven | Attack-driven |
| Automated scanning | Human exploitation |
| Ensures compliance | Simulates real adversaries |
| Surface-level findings | Deep attack path analysis |
| Identifies misconfigurations | Exploits them |
Bottom line:
Audits tell you what might be wrong.
Pen testing shows you what can actually be broken.
What AWS, Azure & GCP Allow You to Test
Each cloud provider has unique testing rules. Here’s what you can (and can’t) test.
AWS Penetration Testing: What’s Allowed
Allowed (no AWS approval required):
- IAM privilege escalation testing
- S3 bucket misconfiguration exploitation
- SSRF → instance metadata access
- EC2 instance exploitation
- Lambda/serverless abuse
- API Gateway exploitation
- CloudFront misconfigurations
- Testing customer-owned applications/services
- Testing customer-controlled network configurations
Not Allowed:
- DoS / DDoS
- Stress testing
- Port flooding
- Attacking AWS-owned infrastructure
- Excessive load generation
Azure Penetration Testing: What’s Allowed
Allowed:
- Azure AD privilege escalation
- Key Vault access testing
- Blob Storage attacks
- Azure VM exploitation
- Azure SQL testing
- App Service endpoint exploitation
- Identity & trust policy review
Not Allowed:
- DoS
- High-volume traffic testing
- Disruptive activities on shared infrastructure
GCP Penetration Testing: What’s Allowed
Allowed:
- IAM role chaining
- Cloud Storage misconfigurations
- Cloud Run/Functions attacks
- VPC firewall bypass attempts
- Privilege escalation across services
Not Allowed:
- Tests that disrupt Google’s shared infrastructure
- Traffic amplification (DoS)
Cloud Pen Testing vs Automated Cloud Tools: Why Human Testing Wins
You’ve probably heard this from vendors:
“Our cloud scanner finds everything a pen test can.”
That’s false — dangerously false.
What Automated Tools (CSPM/BAS) Can Do:
- Detect misconfigurations
- Map assets
- Recommend best practices
- Identify known vulnerabilities
What Automated Tools Cannot Do:
❌ Chain vulnerabilities into real attack paths
❌ Exploit IAM privilege escalation
❌ Abuse real credentials
❌ Test response to adversarial behavior
❌ Simulate realistic ransomware impact
❌ Perform cloud → on-prem lateral movement
What Human Cloud Pen Testers Can Do (and Bluefire excels at):
✔ Identify multi-step privilege abuse
✔ Create novel attack chains
✔ Exploit high-impact misconfigurations
✔ Target business-sensitive data
✔ Validate real-world risk
✔ Simulate real-world cloud attacker TTPs
This is why cloud pen testing is the only way to uncover business-impact vulnerabilities that scanners miss.
Read Our Case Study

Cloud Penetration Testing Pricing (2026)
Cloud testing costs vary based on cloud size, complexity, and the level of threat simulation required.
Typical Price Range (Industry Standard):
- The typical price ranges can be from 2000 USD to 10,000 USD, depending on the scope.

Factors That Affect Pricing:
- Number of AWS/Azure/GCP accounts
- Number of cloud services used
- Identity complexity (IAM/Azure AD)
- Hybrid cloud integration
- API count and sensitivity
- Regulatory requirements (PCI, HIPAA, SOC 2)
- Need for source-code review
- Required threat simulation depth
What You Should Never Pay For
❌ Automated scanning sold as “pen testing”
❌ CSPM configuration checks disguised as offensive testing
❌ Generic reports with no exploit proof
❌ Providers who don’t demonstrate cloud exploitation expertise
Bluefire Redteam’s Cloud Pen Testing Methodology
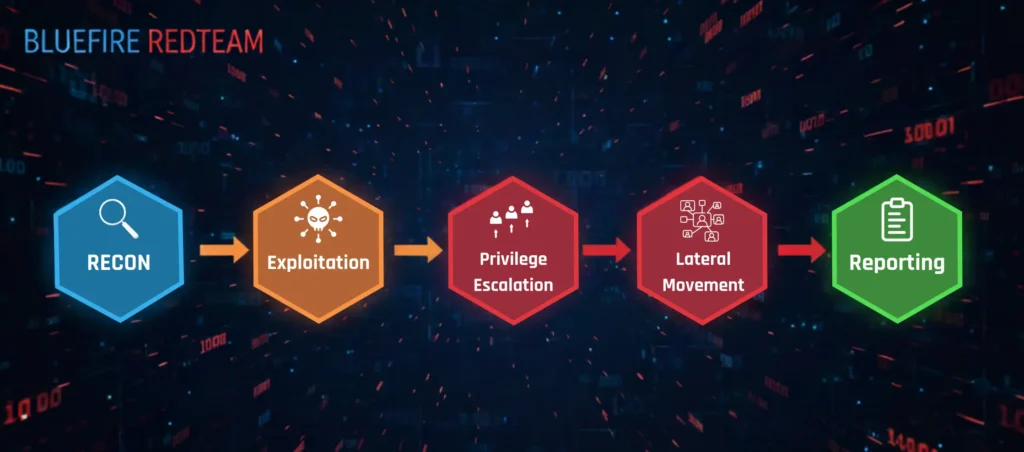
Our method is designed to reflect real attacker behaviour, not compliance checklists.
1. Cloud Recon & Enumeration
We begin by mapping your cloud identity, assets, and exposure points:
- Enumerate IAM roles, policies & trust relationships
- Identify overprivileged accounts
- Analyze VPC architecture
- Identify public-facing assets
- Inventory cloud services (Lambda, S3, EC2, RDS, etc.)
- Detect exposed endpoints & cloud APIs
This forms the attack surface.
2. Misconfiguration Exploitation
This is where 80–90% of cloud breaches originate.
We test:
- Publicly accessible S3/Blob/Cloud Storage
- API Gateway misconfigurations
- Exposed web apps
- Weak secrets stored in cloud metadata
- Insecure serverless functions
- Overly permissive security groups
- IAM trust policy weaknesses
This is where automated tools produce false positives.
Bluefire exploit paths produce proof of compromise.
3. IAM Privilege Escalation Testing
IAM is the heart of cloud security — and the top target of attackers.
We simulate:
- Role chaining
- Abusable IAM actions
- Token theft
- Temporary credential abuse
- Compromised identity scenarios
- Lateral privilege movement
- Dormant privilege path exploitation
This is the most valuable part of a cloud pen test.
It exposes how attackers can escalate from “low” permissions to full admin.
4. Lateral Movement Testing
Cloud lateral movement is subtle and invisible to most detection tools.
Bluefire tests movement paths such as:
- EC2 → RDS
- Lambda → DynamoDB
- Azure VM → Key Vault
- GCP Compute → Cloud Storage
- IAM → CloudTrail tampering
- Cloud → On-Prem (hybrid pivoting)
This simulates a real advanced adversary.
5. Cloud Data Exfiltration Testing
We validate:
- Whether data can leave the cloud undetected
- If logs capture exfil behavior
- If DLP tools block real exploit traffic
- If data can be routed via legitimate services
- If multi-account boundaries stop attackers
This assesses business impact, not just vulnerabilities.
6. Reporting, Remediation & Retesting
Our reports are built for CISOs, engineers, and auditors.
Executive Report Includes:
- Attack overview
- Real-world business impact
- Risk scoring
- Visual attack path diagrams
Technical Report Includes:
- Step-by-step exploitation detail
- Tools and techniques used
- IAM path abuse evidence
- Cloud-native exploit chains
Remediation & Retesting
We verify fixes at no extra cost.
(Not all vendors do this — good pen testing isn’t complete without it.)

Cloud Pen Testing Deliverables
You receive:
- Full cloud attack surface map
- Vulnerability evidence & exploitation details
- IAM privilege escalation pathway maps
- Risk-prioritized remediation guidance
- Cloud architecture security recommendations
- Executive summary for leadership
- Proof-of-exploit screenshots
- Retesting validation report
These deliverables satisfy technical teams, executives, and compliance auditors.
How to Choose a Cloud Pen Test Provider
CISOs should evaluate providers based on:
Technical Cloud Expertise
Do they have real hands-on cloud exploitation experience, not just compliance background?
Offensive Security Focus
Bluefire specializes exclusively in offensive security, not general IT consulting.
Multi-Cloud Capability
AWS, Azure, GCP… most environments are hybrid now.
Evidence-Based Findings
Reports must include exploit chains + evidence.
Methodology Transparency
Real attackers don’t follow checklists — neither do we.
Why Companies Choose Bluefire Redteam for Cloud Pen Testing

Bluefire is trusted by organizations that cannot afford cloud compromise.
Here’s why:
1. Offensive Security is All We Do
We are not auditors or compliance consultants.
We are attackers who think like attackers.
2. Multi-Cloud Exploitation Experts
Our operators specialize in AWS, Azure, and GCP exploitation paths.
3. Real Attack Simulation — Not Scanning
Every test includes:
- IAM abuse
- Lateral movement
- Real exploitation
- Cloud-native attacks
- Hybrid attack simulation
4. Enterprise-Ready Reporting
Clear, concise, actionable, and tailored for both executives and engineers.
5. Retesting Included
We verify remediations — because security isn’t complete without validation.
6. Fast Turnaround & Transparent Pricing
No hidden fees. No vague scopes. No nonsense.
Ready to Strengthen Your Cloud Security?
Your cloud is only as secure as your most exploitable IAM role, weakest API, or misconfigured bucket.
Bluefire’s offensive security team identifies and exploits real weaknesses before attackers do.


