Most global physical security programs are designed around policy consistency, centralized visibility, and standardized facility controls. On paper, this creates uniform protection across global office locations.
In practice, local operational realities often create invisible exposure windows – particularly in high-growth enterprise regions like India.
Over the past several years, multinational organizations expanding operations across India have significantly strengthened baseline controls. However, physical attack paths are increasingly shifting away from traditional perimeter bypass methods and toward operational trust exploitation — including vendor ecosystems, shared facility dependencies, and socially engineered access pathways.
The risk is not that physical security programs are weak.
The risk is that they are misaligned with local attack surface realities.
This report examines the most common physical security blind spots observed in enterprise office environments in India, how these exposures translate into realistic physical-to-cyber attack chains, and how mature global security programs are evolving testing strategies to address them.
Executive Summary
India has become one of the most strategically important enterprise operating regions in the world. Major multinational organizations maintain engineering centers, finance hubs, cloud operations teams, and R&D facilities across cities such as Bengaluru, Hyderabad, Mumbai, Pune, and Gurugram.
These facilities often house:
- Privileged engineering teams
- Cloud access administrators
- Financial systems operators
- Intellectual property repositories
- Customer data environments
While cyber investments in these environments have scaled aggressively, physical security programs have often expanded through replication rather than recalibration.
This creates a structural challenge: global policies built for single-tenant campuses and tightly controlled Western facilities may not fully account for:
- Multi-tenant building environments
- Guard outsourcing models
- High vendor density ecosystems
- Social trust–driven visitor norms
- Rapid office expansion timelines
- Infrastructure adjacency exposure
Physical compromise in India rarely resembles cinematic break-ins. Instead, it frequently involves:
- Tailgating into high-density office floors
- Vendor impersonation
- After-hours badge persistence
- Shared infrastructure reconnaissance
- Informal access escalation
The more critical insight is this:
Modern enterprise physical compromise in India often becomes a cyber event.
Physical entry may enable:
- Device drop campaigns
- Workstation exploitation
- Network cabinet reconnaissance
- Badge cloning for persistence
- Insider-social engineering coordination
This report outlines the structural drivers of these risks, models realistic attack chains in India-specific contexts, and identifies where global security programs tend to overestimate local maturity.
The objective is not alarmism.
The objective is alignment.
Key Findings
- “Policy uniformity does not guarantee enforcement uniformity.”
- “Vendor lifecycle drift is one of the most common hybrid risk multipliers.”
- “Shared commercial infrastructure creates invisible perimeter extensions.”
- “Tailgating success rates often exceed executive expectations.”
- “Physical compromise in India increasingly manifests as cyber initial access.”
- “Guard churn directly correlates with escalation reliability variance.”
- “Board-level risk rarely models physical-to-cloud attack chains.”
- “Testing frequency is significantly lower in India sites than cyber audit frequency.”
- “Rapid expansion often outpaces physical maturity scaling.”
- “Compliance dashboards frequently miss behavioral control degradation.”

Why This Matters to Global Security Leaders
Global Security Directors and CISOs face increasing pressure to demonstrate:
- Program consistency across regions
- Board-level visibility
- Measurable resilience
- Regulatory defensibility
- Converged physical-cyber governance
India presents a convergence environment:
- High operational density
- High trust-based workflows
- High vendor embedding
- High strategic asset concentration
If physical controls are not tested adversarially within this context, the enterprise may unknowingly maintain exposure windows that bridge directly into cyber infrastructure.
Why Global Physical Security Programs Break at Local Sites
Centralized Policy vs Local Enforcement Reality
Global security programs typically standardize:
- Access badge protocols
- Escort policies
- Visitor pre-registration requirements
- Guard post orders
- Incident escalation trees
However, enforcement depends on:
- Guard training continuity
- Cultural challenge norms
- Supervisor oversight
- Site-level operational tempo
- Shift fatigue management
India’s guard ecosystem frequently operates through third-party agencies. While professional and structured, these agencies often face:
- High staff turnover
- Wage compression
- Training variability
- Multi-site rotation
- Limited integration into global SOC structures
The result is not incompetence.
It is variability.
That variability introduces enforcement drift.
A centralized policy mandating zero tailgating may exist – but peak-hour social accommodation behavior often overrides rigid enforcement.
Centralized metrics often measure documentation compliance rather than real-world enforcement consistency.

Shared Building & Shared Security Vendor Risk
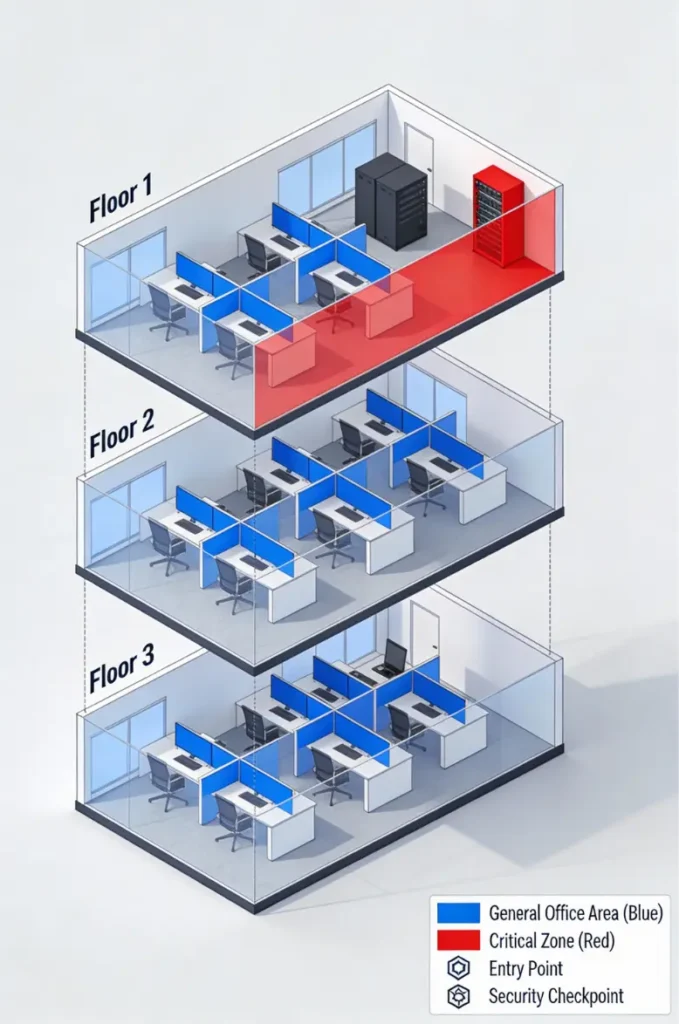
Many enterprise facilities in India operate within:
- Tier 1 IT parks
- SEZ zones
- High-rise shared commercial towers
- Mixed-use complexes
Shared building characteristics include:
- Lobby security controlled by landlord
- Shared CCTV systems
- Shared HVAC and maintenance corridors
- Shared parking infrastructure
- Shared telecom routing
This creates a layered control dependency.
Tenant-level controls may be robust.
Building-level enforcement may not match the same maturity.
Risk shifts from perimeter breach to blending.
Vendor Ecosystem Risk Multiplication
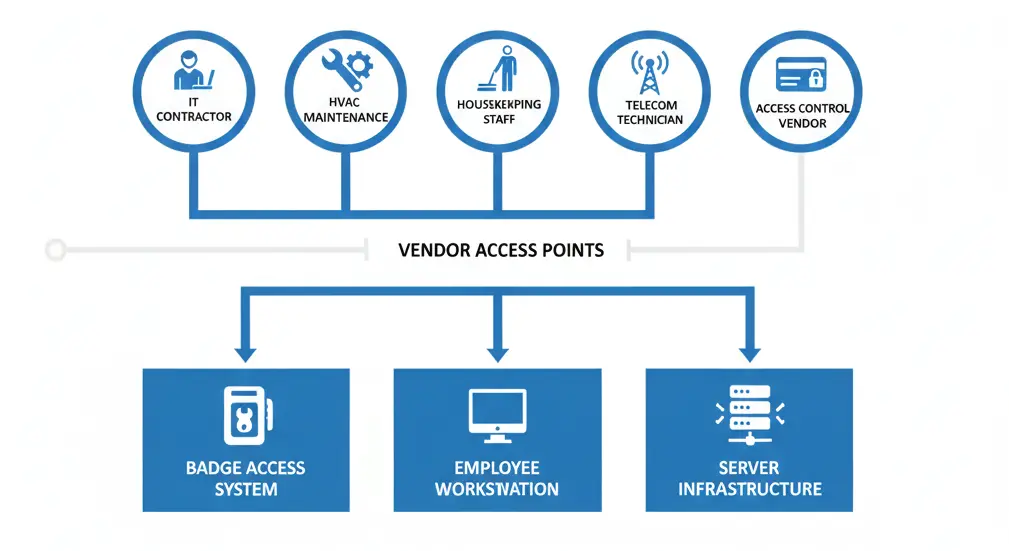
India enterprise environments often embed:
- IT support contractors
- Telecom technicians
- Structured cabling vendors
- HVAC maintenance teams
- Pantry staff
- Housekeeping personnel
- Access control integrators
Each vendor relationship introduces:
- Badge issuance
- Access level designation
- Revocation timing dependency
- Background screening variability
In high-scale environments, vendor access often exceeds employee access counts.
Without synchronized identity lifecycle governance, vendor ecosystems become cumulative risk multipliers.
India-Specific Enterprise Physical Attack Surface Factors
Guard Outsourcing & Training Variability
India’s guarding ecosystem is structured and professional — yet high turnover is common due to:
- Market wage pressures
- Inter-site movement
- Seasonal rotation
- Contract renewals
Frequent rotation impacts:
- Familiarity with escalation trees
- Confidence in challenging senior personnel
- Awareness of threat scenarios
- Alignment with global security philosophy
In adversarial testing scenarios, inconsistent challenge behavior is frequently observed.
Visitor Culture & Social Trust Norms
Corporate hospitality norms in India prioritize accommodation and politeness.
High visitor categories include:
- Candidates
- Consultants
- Vendors
- Delivery staff
- Senior management guests
Escalation friction may be perceived as disrespectful.
This impacts:
- Tailgating prevention
- Escort adherence
- Badge visibility enforcement
- Identity re-verification
Trust is culturally reinforced – which attackers exploit.
Vendor Trust Chains & Informal Access Expansion
Vendor presence often becomes normalized.
Informal expansion patterns include:
- Repeated temporary access becoming semi-permanent
- Verbal extension approvals
- Shared badge lending in maintenance contexts
- Supervisor override approvals without documentation
Trust chains extend beyond formal documentation.
Rapid Office Expansion Security Maturity Gaps
India enterprise growth often moves quickly.
Rapid expansion may result in:
- Security staffing lag
- Incomplete SOP harmonization
- Delayed access control integration
- Vendor onboarding at scale without lifecycle mapping
Security maturity may trail operational expansion.

Realistic Physical-to-Cyber Enterprise Attack Paths (India Context)
Scenario 1: Vendor → Workstation → Domain Pivot
An IT vendor with recurring access is observed working unsupervised in a collaboration zone.
Opportunity window:
- Unlocked workstation
- USB payload insertion
- Credential harvesting
- Lateral movement
Physical access becomes domain compromise.
Scenario 2: Tailgating → Device Drop → Persistence
High-density floors in Bengaluru often feature open seating.
An actor tailgates during shift change.
Drops small device under desk cluster.
Device initiates beaconing.
Initial access established without perimeter breach.
Scenario 3: Badge Cloning → After Hours Access
Employee badge template captured visually.
Cloned through low-cost hardware.
After-hours entry achieved when guard vigilance decreases.
Data center adjacency exploited.
Scenario 4: Insider + External Social Engineering
External actor coordinates with disgruntled insider.
Insider provides timing patterns.
External actor blends during peak flow.
Recon conducted without raising alarm.

Where Global Security Programs Overestimate Local Maturity
| Assumption | Observed Gap |
|---|---|
| Escort policy enforced | Drift during peak periods |
| Vendor lifecycle automated | Manual dependency delays |
| Multi-tenant lobby secure | Landlord-level variance |
| After-hours strictly monitored | Reduced staffing vigilance |
| Guard escalation consistent | Training variability |
Compliance metrics often fail to capture behavioral variance.
Building Types That Drastically Change Risk in India
Tier 1 Tech Parks
High density, shared infrastructure, mixed tenant risk.
Shared Commercial Towers
Vertical movement complexity, lobby dependency risk.
Hybrid Campuses
Mixed leased and owned control confusion.
Legacy Converted Offices
Retrofitted infrastructure, cable adjacency exposure.
What Mature MNC Security Teams Are Testing in 2026
- Full attack chain simulation
- Insider blending
- Vendor impersonation
- Low-noise multi-visit reconnaissance
- Tailgating telemetry measurement
- Physical-to-cyber pivot validation
Advanced programs measure outcome, not assumption.
Board-Level Risk Translation
Physical breach → workstation access → domain pivot → ransomware event → regulatory exposure → brand impact → stock volatility.
Physical security is not facilities management.
It is enterprise risk governance.
India Physical Security Readiness Self-Assessment Checklist
- Have India sites undergone adversarial physical testing?
- Are vendor badges time-bound?
- Is badge revocation synchronized with VPN disablement?
- Is tailgating measured or assumed?
- Are multi-tenant dependencies modeled?
- Is shared infrastructure access reviewed?
- Are guards escalation-tested?
- Is visitor device policy enforced?
- Is after-hours access monitored?
- Are hybrid attack chains tabletop tested?
When Enterprises Should Prioritize India Physical Testing
Triggers include:
- Rapid headcount growth
- New tech park move-in
- M&A integration
- Vendor ecosystem expansion
- High-value R&D presence
- Board audit inquiry
- Cyber incident with unknown root cause
- Regulatory scrutiny
- Guard agency transition
Conclusion + Industry Outlook
India’s enterprise footprint will continue expanding.
Physical attack methods are evolving toward trust exploitation and infrastructure blending.
The question for global leaders is no longer:
“Do we have a physical security policy?”
It is:
“Have we tested whether our global security intent survives India’s operational reality?”
Organizations that converge physical and cyber adversarial testing will outpace those relying on compliance dashboards.
India is not a weak link.
It is a convergence environment.
And convergence environments require adversarial validation.

